Enterprise Open Source Software Solutions for the Public Sector
Red Hat's innovative software solutions empower Public Sector teams to ensure collaborative excellence, uncompromising quality and airtight security. From standardizing operating systems to simplifying complex workloads with automated processes and cloud-native app development, Red Hat accelerates mission-critical objectives with unparalleled flexibility, scalability and security.
Carahsoft has served as Red Hat’s master Government IT aggregator and distributor for more than 20 years, providing Government, Education and Healthcare organizations with access to industry-leading enterprise open source software solutions, services and support. Carahsoft delivers Red Hat’s full solutions portfolio to help our customers solve for today’s most pressing MultiCloud, AI/ML, Cybersecurity, DevSecOps and IT Modernization challenges, at the best possible value.
Red Hat’s Master Government Aggregator and Distributor Since 2005
Carahsoft holds a portfolio of contract vehicles to streamline Red Hat IT procurement for our customers across the U.S. and Canadian Public Sectors. Whether you're investing in automation, containers, cloud or security, Carahsoft ensures a seamless buying experience, on your timeline. Carahsoft's CarahCloud Marketplace, a digital catalog for third-party software products and solutions in AWS Marketplace, also offers a streamlined path for public sector IT procurement - simplifying the buying process through pre-negotiated contracts. From bundled offerings to flexible deployment options, CarahCloud is built to support your IT priorities. You can request Red Hat pricing for all Cloud Marketplaces via this webpage.
Build on a Reliable Foundation with Red Hat Enterprise Linux
Red Hat Enterprise Linux (RHEL) is the leading enterprise Linux platform for standardizing IT infrastructure, certified on hundreds of clouds and with thousands of hardware and software vendors. From the public cloud to the edge, Red Hat's operating system provides scalability for existing apps across bare-metal, virtual, container and multicloud environments. Discover how to maximize uptime, mitigate threat incidents and instantly adopt new features while enhancing performance for modern AI/ML workloads across distributed IT ecosystems.
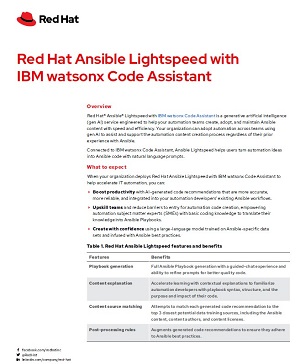
Automate and Secure IT Operations with Red Hat Ansible Automation Platform
Red Hat Ansible Automation Platform is an enterprise framework for building and operating IT automation at scale, from hybrid clouds to the edge. Enable seamless, enterprise IT automation across your organization by accelerating mission-critical workflows and integrating AI with existing systems for enhanced efficiency. Explore the resources to discover how Ansible Automation reduces manual processes while improving IT management, security and compliance through standardization.
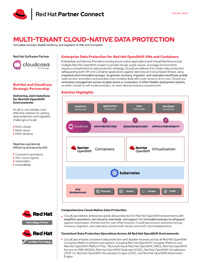
Deploy Workloads Across Any Cloud Environment
Red Hat’s open hybrid cloud approach increases interoperability across hosted and managed data services and platforms, optimizing application performance, scalability and security. Red Hat OpenShift Container Platform (OCP) is a unified, enterprise-ready Kubernetes container platform with full-stack automated operations that improve developer productivity and promote innovation at scale, optimized for managing hybrid and multicloud deployments. By leveraging OpenShift, Public Sector teams can effectively integrate AI-driven analytics, DevSecOps automation and cross-domain data visibility. Reduce operational costs by simplifying cloud-native application development and delivery with open hybrid cloud architecture.
Accelerate AI-Powered Development with Red Hat OpenShift AI
Red Hat OpenShift AI is a flexible MLOps platform that empowers IT teams to standardize and streamline their processes for introducing machine learning into their applications. Built on a secure foundation of Red Hat Enterprise Linux and OpenShift, this solution provides a robust and trusted environment for the development and deployment of machine learning models at scale.
Redefining Automation and Scale with Red Hat OpenShift Virtualization
By unifying Virtual Machines (VMs) and containers with Red Hat OpenShift Virtualization, IT teams can simplify their infrastructure, improve efficiency, reduce costs and drive innovation. OpenShift Virtualization enables VMs to streamline application workloads by leveraging robust AI models that increase productivity and security capabilities.
Connect with a Red Hat Specialist
Click the button below to schedule time with your dedicated Red Hat representative and learn how Carahsoft and Red Hat can help your IT organization identify the best-fit solution for your unique IT requirements.