Unknown Cyber Solutions for the Public Sector
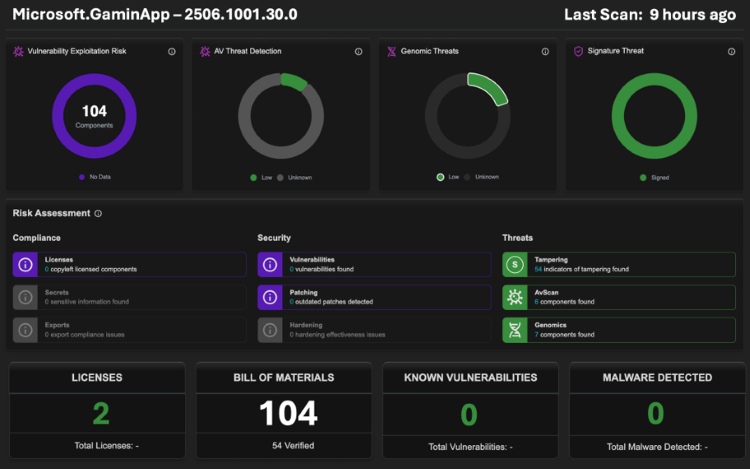
Unknown Cyber Software Scan™ for Software Procurement, Compliance and Risk Management
Reduce third-party software risk and meet Zero Trust, ATO and CMMC 2.0 compliance requirements, beyond attestation by technically verifying vendor supplied software and firmware through Deterministic Binary Composition Analysis.
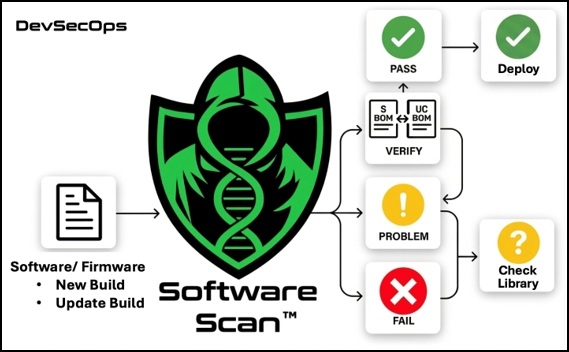
Unknown Cyber Software Scan™ for Software Development
Protect Pipelines with deterministic binary analysis that mathematically inspects every function to find third-party code and phantom dependency risks beyond SCA and QA checks so teams can confidently ship code alongside a verified SBOM.

UC Threat Intelligence
Hunt forward with an information advantage. Use automated, customized YARA rules that target functional logic—rather than relying on superficial strings or transient IOCs.

UC Services
Explore our full range of professional services. Partner with UC experts for rapid jumpstarts, staff augmentation, custom AI integrations, compliance advisory, and fully managed pipeline and thrid-party software assessment.

