Software Scan™ for Software Procurement, Compliance, and Risk Management
Reduce third-party software risk and meet CMMC 2.0, ATO, and Zero Trust compliance requirements—beyond attestation—by technically verifying vendor-supplied software and firmware through Deterministic Binary Composition Analysis.
Assess software capability before it runs
Federal agencies and prime contractors are under increasing pressure to verify the integrity and security of software received from external vendors. In modern software supply chain attacks, adversaries are actively compromising third-party dependencies and weaponizing AI to rapidly discover vulnerabilities, generate functional exploit code, and automate multi-stage attacks at machine speeds. Traditional tools are often blind to implants, AI-generated exploits, and sophisticated tampering.
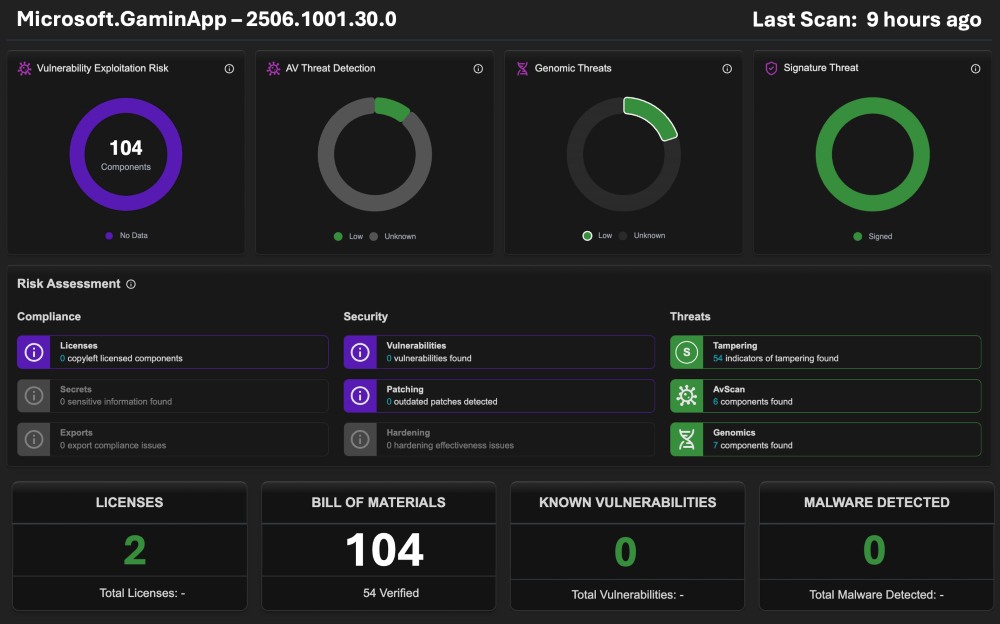
Unknown Cyber Software Scan™ delivers a revolutionary automated approach to software supply chain security, leveraging Deterministic Binary Composition Analysis (BCA). Going beyond traditional tools, UC's platform analyzes the "DNA" of binary code to detect hidden threats in third-party, COTS, and open-source software without requiring source code—helping federal buyers build trust before approving, acquiring, or deploying software.
Gartner® “Perform binary composition analysis (BCA) on critical and high-risk software to validate supplier SBOM completeness and detect additional supply chain risks..”
Designed for Procurement, Compliance & Risk Management Teams
Meets: EO 14028, EO 14306, NIST SP 800-218 (SSDF), NIST SP 800-171 Rev 3, NIST IR 8397, NIST SP 800-161, CMMC 2.0, OMB M-22-18, FedRAMP/ATO & CISA KEV.
Key Benefits:
- Audit-Ready Risk Controls: Generate verifiable records for compliance audits—no black box.
- Supply Chain Compensating Controls: Verify third-party software to generate technical evidence for federal mandates.
- Recursive Inventory: Map components and dependencies for continuous monitoring, maintaining an active, auditable inventory.
- Known & Undeclared Vulnerability Analysis: Find functional risks by matching N-day logic to undetected threats within software through Genomic Analysis.
- Independent SBOM Validation: Build a recursive inventory of dependencies to verify a vendor's declared SBOM against actual compiled code.
- Pre-Deployment Assurance: Validate software before production to reduce risk, providing automated verification to accelerate ATO timelines.
- Firmware and Software Monitoring: Continuously monitor baselines and update version deltas to inspect for capability changes and detect drift.
- License Compliance: Detect risks to avoid IP issues by analyzing proprietary and open-source licenses to meet federal procurement standards.
- Signature & Provenance Verification: Validate digital certificates to ensure binaries are legitimately signed and provide proof of provenance.
- Binary Composition Analysis (BCA): Analyze register and memory effects on CPU of every byte-code function to identify hidden risks.
- Anti-Tamper Verification: Identify unauthorized changes, injected payloads, and post-build manipulation via deep binary analysis in all files.
- Advanced Threat Hunting: Use automated, customized YARA rules to target functional logic. Hunt for the immutable TTPs identified within register and memory effects on the CPU—rather than relying on superficial strings or transient IOCs.
Built for New Public Sector Security Requirements for Critical Infrastructure & DIB
As federal policies shift away from self-attestation toward verifiable technical controls, prime contractors and agencies must inspect third-party binaries and need a method to enforce auditable evidence of flow-down compliance. By mapping the exact memory and register effects of every byte-code function, Software Scan™ equips procurement, compliance, and IT risk teams with unparalleled visibility into the capabilities of the “software itself.” This automated deep visibility is now possible through Unknown Cyber’s breakthrough DARPA Cyber-genome technology. Whether inspecting contractor-delivered packages or validating vendor updates, Software Scan™ delivers deep analysis of compiled code to assess and uncover hidden, uncontrolled, and unmitigated risks that conventional tools completely miss.

