Software Supply Chain Security (SSCS) -with Deterministic Visibility
Unknown Cyber delivers deterministic visibility into every function within your software and updates, offering unmatched accuracy, speed, and scale—even when there is no source code available.
The vendor trust model is broken. In a world rapidly adopting and creating AI-generated code, procurement compliance has extended beyond attestation to technical verification. To help customers meet these mandates, Unknown Cyber performs Deterministic Binary Composition Analysis (BCA)—a mathematically grounded innovation beyond traditional BCA, which Gartner recommends using to validate SBOMs, identify provenance, and detect additional supply chain risks (e.g., malicious code). Unknown Cyber considers software capability as procurement criteria. Crucially, our deterministic analysis identifies threats missed by heuristic, probabilistic LLM, or higher-level file structure analysis methods that do not consider the capability of the software itself.
By enabling customers to not only trust but verify their mission-critical software, we automate auditable compliance for CMMC 2.0, NIST Executive Orders , 33 CFR Part 101, Subpart F, and strict Zero Trust mandates. This allows federal agencies to rigorously verify the third-party software they procure and inspect. We also equip internal developers to confidently secure final builds that rely upon open-source and third-party libraries, replacing assumed vendor trust with mathematical certainty.
Software Scan™ for Procurement
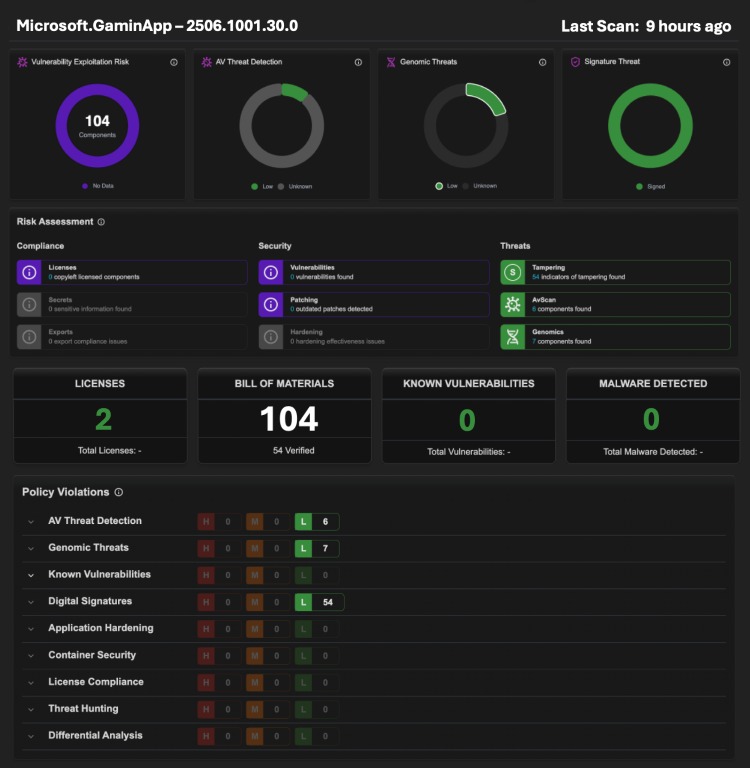
Unknown Cyber’s Software Scan™ offers a revolutionary, deterministic approach to verify third-party software upon delivery, directly answering Gartner’s call to perform Binary Composition Analysis (BCA) on high-risk software. Powered by DARPA-developed genomic analysis, it mathematically computes the ultimate effects of every function on registers and memory. This means compliance professionals, risk managers, and leaders can achieve unprecedented, auditable accuracy regarding exactly what is inside their vendors' binaries, without ever needing the proprietary source code. By moving from probabilistic guesswork to deterministic truth, organizations can embed continuous monitoring into procurement, establish a verifiable Zero Trust posture, and confidently meet CMMC 2.0 mandates.
SSCS for Purchasers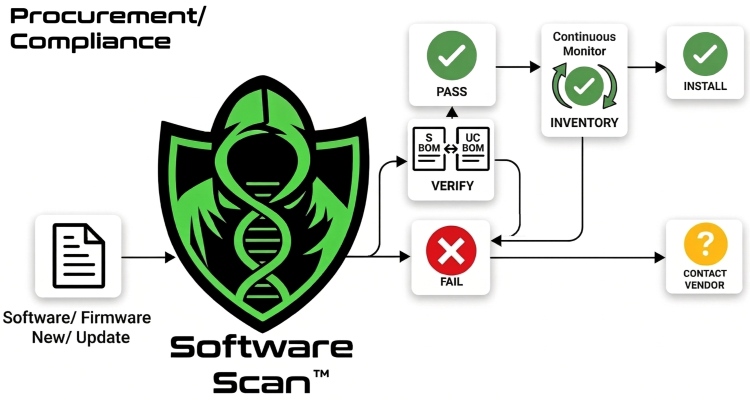
Software Scan™ for DevSecOps
In the modern development landscape of AI-generated code and complex open-source dependencies, pipelines are increasingly exposed to third-party risk. Traditional software composition analysis (SCA) tools routinely miss these threats when the software functions as expected, ignoring unseen capability hidden from developers that is designed to defeat QA controls. The limited visibility of SCA is demonstrated in research that shows manifest-based SCA can miss up to 50% of the components actually present in a final, compiled binary. Such tools are often blind to phantom dependencies. Powered by DARPA-developed genomic analysis, Software Scan™ seamlessly integrates into your workflow to mathematically inspect every function. We also analyze third-party libraries from npm, pip, Maven, Cargo, and other ecosystems. Software Scan™ instantly flags unreported vulnerabilities, unreported malware, polymorphic malware, and hidden native binaries that bypass standard security tooling. This means DevSecOps teams and engineering leaders can achieve an unprecedented depth of visibility using Deterministic BCA that provides auditable accuracy. It automatically inventories exactly what is inside their final builds and documents invisible dependencies. By moving beyond probabilistic tools that model patterns, file structure, or compare metadata, to Unknown Cyber’s mathematical truth, organizations can automatically identify compromised pipelines, automate Secure by Design principles, establish verifiable Zero Trust controls, and confidently ship code alongside a verified SBOM generated with every analysis.
SSCS for DevelopersUpcoming Events
|
Virtual Event
 |
Procuring in the Dark: Unmasking Hidden Risks in AI-Generated and Third-Party Software
Hosted By: Unknown Cyber & Carahsoft
|







