Software Scan™ for Development
Embed mission assurance into every software release with advanced binary composition analysis that not only detects threats but also tells you what changed and why it matters.
Federal teams face increasing pressure to deliver software rapidly while ensuring integrity, trust, and compliance. Although traditional AppSec tools (like SAST, DAST, and IAST) identify surface-level risks, they stop at the source code and lack visibility into hidden capabilities or phantom dependencies within the software build.
Unknown Cyber Software Scan™ empowers DevSecOps teams to move fast without sacrificing trust. By mathematically proving the integrity of each function through deterministic binary analysis on final build artifacts, it provides unmatched visibility into the software supply chain—without slowing down release cycles. Going beyond point-in-time detection, Software Scan™ continuously analyzes successive binary versions along with third-party packages to determine how changes alter functionality.
Why Scan Package Binaries?
Packages can include pre-compiled native binaries and executable scripts. While often legitimate, hidden functionality poses unique security risks.
Go Beyond Detection: Understand Software Intent
Unlike tools that only scan static artifacts, Unknown Cyber introduces Genomic Binary Analysis™—a proprietary approach that evaluates software and firmware at the function level across versions, uncovering hidden risks that increasingly go undetected.
Key Capabilities
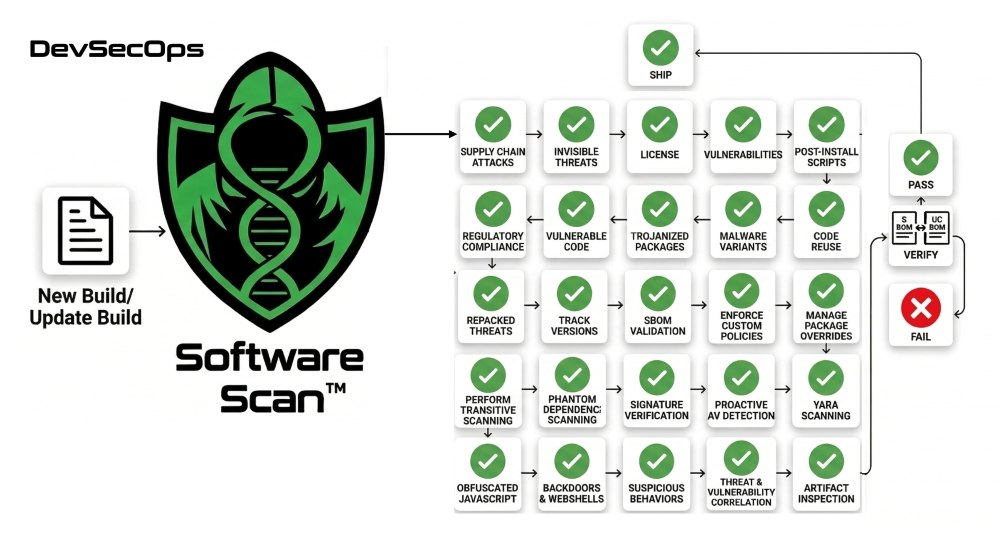
Software Scan™ adds multiple layers of security analysis to detect threats that traditional SCA and QA tools miss:
- Supply Chain Attacks: Malicious binaries injected into popular packages can execute arbitrary code during the build, install, or other development stages.
- Invisible Threats: Native code bypasses JavaScript-based security scanners.
- License Compliance: Native binaries may carry different licensing terms.
- Vulnerability Gaps: Memory-unsafe languages (C/C++) can have vulnerabilities not caught by JavaScript tooling.
- Post-Install Scripts: Scripts in pre-install/post-install hooks can execute malware.
- Regulatory Compliance: SBOM requirements (EO 14028, NTIA) demand visibility into all software components.
Genomic Similarity Analysis
Beyond signature-based detection, Unknown Cyber analyzes each function within executables and calculates a mathematical proof of software DNA. This detects:
- Vulnerable Code: Libraries with known CVEs reused across packages.
- Trojanized Packages: Malicious code injected between versions—a common supply chain attack TTP. By tracking code across successive versions, Unknown Cyber can detect when legitimate packages are compromised—identifying the exact code changes that introduce backdoors or malware, even when attackers try to hide modifications in otherwise normal updates.
- Zero-Day Threats: Even if a file is brand new and has zero AV detections, genomic analysis can match its functionality to known threats—catching attacks before they are publicly disclosed, such as N-day vulnerabilities repurposed as zero- day threats that utilize the same TTPs visible in their functions.
- Malware Variants: Threats that haven't been cataloged yet, as well as polymorphic malware or code that mutates to evade signatures.
- Repacked Threats: Known malware hidden in new wrappers.
- Code Reuse: Components borrowed from known malicious families.
Dependency Inventory, SBOM & Audit Compliance
Beyond security scanning, uploading to Unknown Cyber builds a centralized inventory of all third-party packages across your organization's repositories. Each file is tagged with the package name, version, and source repository—giving you a single source of truth for dependency tracking.
- Know What's Deployed: See all third-party components across projects.
- Track Versions: Monitor which versions are in use, including in released software.
- Meet SBOM Regulations: Comply with requirements like Executive Order 14028, NTIA guidelines, and customer audits.
- Enforce Custom Policies: Define your own allowed/warning/denied lists.
- Manage Package Overrides: Approve specific packages after review.
- Perform Transitive Scanning: Check nested dependencies, not just direct ones.
Comprehensive Security Scanning
- License Compliance: Automatically scans all packages for license compatibility issues.
- Code Signature Verification: Validates digital signatures on executables.
- Beyond Antivirus Detection: Every function is genomically cataloged and cross-referenced against 70+ antivirus engine verdicts. This function-level, multi-engine approach identifies threats that individual scanners miss, ensuring comprehensive detection with minimal false negatives.
- YARA Scanning: Detects obfuscated JavaScript, crypto miners, backdoors, webshells, and suspicious behaviors like process injection.
Advanced DevSecOps Coverage
- Mission Deviation Analysis: Identify how package updates change software behavior and assess whether those changes align with intended capabilities.
- Genomic Binary Comparison: Compare successive builds to detect subtle or obfuscated changes.
- Threat & Vulnerability Correlation: Map the mathematically computed functional identity of flaws—beyond version metadata—to automatically impute known vulnerabilities, identify malware patterns, and match N-day threats to zero- day exploits through shared functional TTPs.
- Deep Artifact Inspection: Analyze compiled binaries, containers, firmware, and system images beyond source-code limitations.
- CI/CD Integration at Scale: Automate validation and enforcement with API-driven workflows across DevSecOps pipelines.
- Advanced Workflow Coverage: Inspect AI/ML models, LLM artifacts, and virtualized environments.
- Compliance Alignment: Supports EO 14028, NIST 800-218 (SSDF), and Secure by Design initiatives.
Built for Mission-Critical Environments
From civilian agency teams to national labs and defense contractors, organizations rely on Software Scan™ to catch hidden risks early. By embedding this intelligence directly into the DevSecOps process, agencies can reduce rework, streamline approvals, and maintain continuous trust.
Why Unknown Cyber?
By combining deterministic binary analysis with mission-aware intelligence, Unknown Cyber delivers a new category of software assurance:
- From point-in-time scans ➔ to continuous evolution tracking.
- From vulnerability awareness ➔ to functional risk insight.
Ensure Software Integrity Across Every Release
Embed build-time assurance into secure DevSecOps pipelines with binary analysis that detects hidden risks, validates integrity, and enforces compliance before deployment.

