Runtime Integrity Verification for the Public Sector
Invary extends Zero Trust to the system layer by continuously verifying Runtime Integrity.
Powered by technology exclusively licensed from the NSA's Laboratory for Advanced Cybersecurity Research, Invary exposes unauthorized system changes without relying on signatures or behavioral patterns.
Detecting AI-Driven and Zero-Day Attacks Bypassing EDR/XDR
AI-driven and zero-day attacks operate without prior indicators, targeting the operating system that is assumed trustworthy. When the system generating telemetry is compromised, every control built on it becomes unreliable and security decisions degrade.
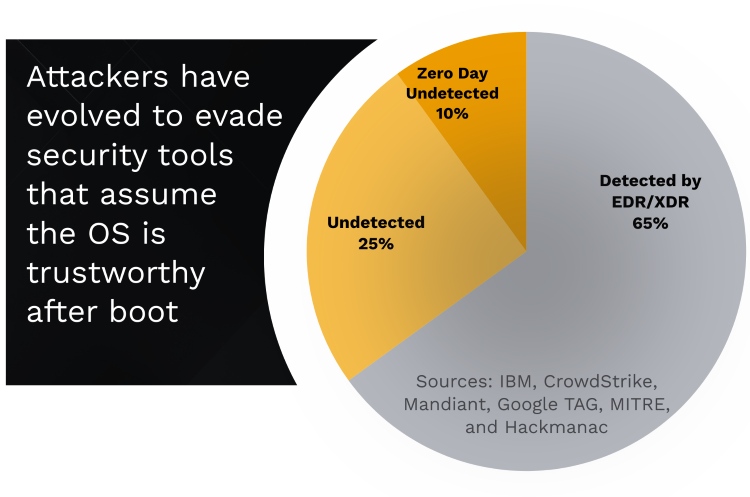
Public sector organizations managing sensitive data and mission-critical systems require verified assurance to detect what EDR/XDR cannot, protect existing security investments, reduce breach risk, and maintain operational continuity.

In-Memory Integrity Verification
Invary validates whether systems are operating as intended and exposes unauthorized change directly, regardless of technique. This restores confidence in the data on which security teams and leaders depend.
Verification Throughout the Security Lifecycle
Before incidents, Invary confirms systems remain uncompromised. During response, teams make decisions based on verified conditions. After remediation, organizations confirm systems have returned to known good states. For public sector security teams, this means faster investigations, improved people efficiency, protected security investments, and reduced impact.
Invary’s Runtime Integrity, Powered by NSA-Licensed Technology
- Runtime Integrity Verification - Continuous validation that detects unauthorized system modifications without signatures or behavioral analysis
- EDR/XDR Bypass Detection - Exposes advanced attacks that bypass traditional endpoint security through novel techniques or AI-generated variants
- Incident Response and Recovery Validation - Verifies system conditions during active response and confirms successful remediation without assumptions
- Government and Critical Infrastructure Security - Proven deployments in government agencies, education, and critical infrastructure

Zero Day Detection
Reveals advanced kernel-level attacks that evade existing security tools

Data Privacy and Security
Verifies & attests to system integrity and data privacy in real time

Zero Trust Architecture
Applies Zero Trust principles by removing implicit trust of the OS

Audit and Compliance
Provides evidence to enhance efforts: SOC2, FedRAMP, CMMC, ATO, etc
Implementation
Invary integrates with existing security operations and supports Windows and Linux deployment without replacing current tooling. Available as SaaS or on-premise deployment model, Invary covers attack classes that bypass traditional defenses while maintaining operational continuity.
Invary for Public Sector Organizations
Invary provides the continuous system integrity verification layer that results in fewer breaches, reduced disruption, and defensible security decisions.