Global Cybersecurity Best Practices Community
The Center for Internet Security® (CIS®) makes the connected world a safer place for people, businesses, and governments through our core competencies of collaboration and innovation. CIS is a community-driven nonprofit, responsible for the CIS Critical Security Controls® and CIS Benchmarks®, globally recognized best practices for securing IT systems and data. CIS leads a global community of IT professionals to continuously evolve these standards and provide products and services to proactively safeguard against emerging threats.
CIS Hardened Images® provide secure, on-demand, scalable computing environments in the cloud. CIS is home to the Multi-State Information Sharing and Analysis Center® (MS-ISAC®), the trusted resource for cyber threat prevention, protection, response, and recovery for U.S. State, Local, Tribal, and Territorial government entities.
Secure Cloud Infrastructure with CIS Hardened Images®
CIS Hardened Images® help organizations reduce cloud risk and deploy secure infrastructure faster with preconfigured virtual machines aligned to CIS Benchmarks®. Available across major cloud platforms, Hardened Images reduce configuration drift, accelerate audit readiness, and simplify secure cloud adoption.
Strengthen SLTT Cybersecurity with CIS Services®
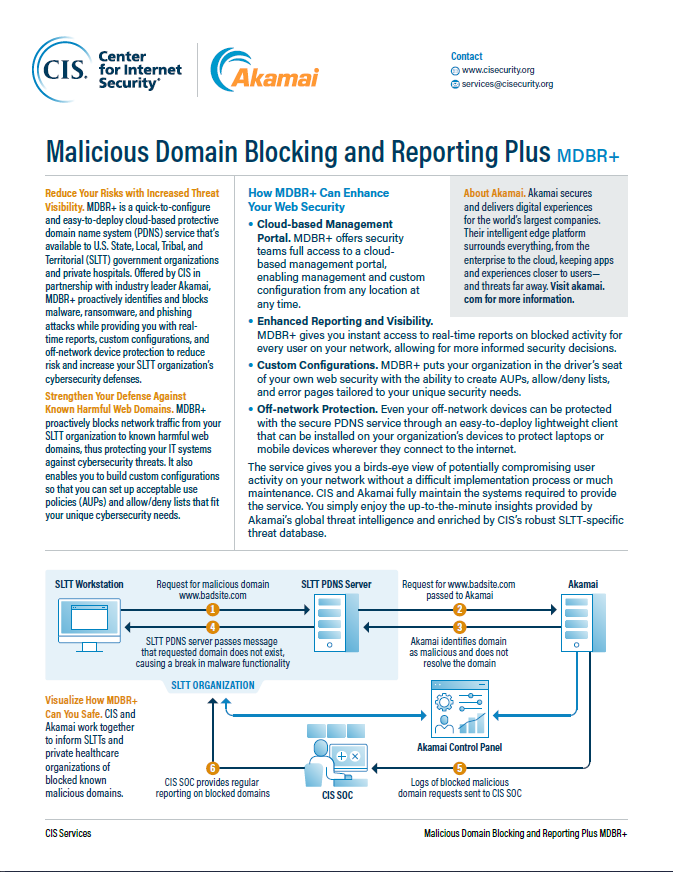
CIS Services® provides specialized expertise to support U.S. State, Local, Tribal, and Territorial (SLTT) entities to augment a defense-in-depth approach for cybersecurity. Many of these cost-effective solutions include 24x7x365 monitoring and management through CIS's U.S.-based Security Operations Center (SOC) as well as incident response support.
Implement CIS Controls with CIS SecureSuite®
CIS SecureSuite provides thousands of organizations with access to an effective and comprehensive set of cybersecurity resources and tools to implement the CIS Critical Security Controls (CIS Controls) and CIS Benchmarks. Track compliance with industry frameworks, secure systems with more than 100 configuration guides, and more, all with one powerful Membership.