AVAILABLE 24x7
888.662.2724
AVAILABLE 24x7
(888) 66CARAH
Fast & Accurate
Request A Quote
Quick Response
Chat With Us
Carahsoft, in conjunction with its vendor partners, sponsors hundreds of events each year, ranging from webcasts and tradeshows to executive roundtables and technology forums.
Events and Resources
Events
Upcoming Events

Zoom Onsite Event
Event Date: June 09, 2026 - June 11, 2026
Hosted By: Consortium of Liberal Arts Colleges
Hosted By: Consortium of Liberal Arts Colleges
Join Zoom at the CLAC conference '26! This is an exclusive leadership event designed to bring together members of our consortium to support thought leadership in higher education information technology. Unlike traditional technical conferences, CLAC focuses on managing and leading—exploring how emerging ...

Zoom Onsite Event
Event Date: June 10, 2026 - June 11, 2026
Hosted By: Conference on Higher Education Computing in Kansas
Hosted By: Conference on Higher Education Computing in Kansas
Join Zoom at CHECK '26! This exceptional opportunity brings IT professionals together to connect, learn, and network, thanks to our incredible sponsors, whose support makes this conference possible. Don’t miss out! Join your peers and sponsors as they dive into the cutting-edge world of innovation and ...

Zoom Onsite Event
Event Date: June 10, 2026 - June 11, 2026
Hosted By: Utah Education Network
Location: Cottonwood Heights, UT
Hosted By: Utah Education Network
Location: Cottonwood Heights, UT
a {
text-decoration: none;
color: #464feb;
}
tr th, tr td {
border: 1px solid #e6e6e6;
}
tr th {
background-color: #f5f5f5;
}
On June 10th–11th, Zoom will attend the UEN Tech ...
Raise by Mission Cultivate Virtual Event
Event Date: June 16, 2026
Hosted By: Raise by Mission Cultivate & Carahsoft
Hosted By: Raise by Mission Cultivate & Carahsoft
Join Carahsoft and Mission Cultivate on June 16th for an exclusive webinar where government insiders, industry practitioners and funding strategists will break down how the funding environment really works and what top organizations do differently to stay ahead.

Multi-Vendor Onsite Event
Event Date: June 25, 2026
Hosted By: Udemy, Workera & Carahsoft
Location: Reston, VA
Hosted By: Udemy, Workera & Carahsoft
Location: Reston, VA
Join our Udemy, Workera, and Carahsoft lunch & learn, bringing together public and private sector workforce leads and AI practitioners.
Expect a high-impact conversation on measuring and closing the AI readiness gap across your organization.

HashiCorp Virtual Event
Event Date: July 09, 2026
Hosted By: HashiCorp & Carahsoft
CPE credit available
Hosted By: HashiCorp & Carahsoft
CPE credit available
Federal bureaus face relentless pressure to roll out new digital services quickly while safeguarding highly sensitive data and meeting strict FedRAMP, FISMA and audit mandates.
At the same time, agencies are expected to operate across an increasingly complex mix of ...

AMSimpkins and Associates Onsite Event
Event Date: April 07, 2027 - April 09, 2027
Hosted By: AMSimpkins & Associates
Location: Atlanta, GA
Hosted By: AMSimpkins & Associates
Location: Atlanta, GA
The SecureED Conference is the premier national gathering for institutions committed to protecting enrollment integrity and preventing student application and financial aid fraud. We unite higher-education leaders, technology teams, and compliance professionals to share proven strategies, real-world ...
Archived Events

Informatica Virtual Event
Event Date: June 04, 2026
Hosted By: Informatica & Carahsoft
Hosted By: Informatica & Carahsoft
As higher education institutions face increasing pressure to modernize and deliver trusted insights, data integrity has become a persistent challenge. Legacy systems and siloed data sources create inconsistent constituent records, limit visibility and introduce risk directly threatening large-scale transformation ...

Asana Onsite Event
Event Date: June 03, 2026
Hosted By: EDUCAUSE
Hosted By: EDUCAUSE
a {
text-decoration: none;
color: #464feb;
}
tr th, tr td {
border: 1px solid #e6e6e6;
}
tr th {
background-color: #f5f5f5;
}
Project management tools give education teams the clarity ...
OpenAI Virtual Event
Event Date: June 02, 2026
Hosted By: OpenAI & Carahsoft
Hosted By: OpenAI & Carahsoft
This OpenAI Codex webinar taught attendees how educational institutions can use Codex to build practical internal workflows, reduce repetitive work and become more efficient across day-to-day operations. This session was designed for both technical and non-technical audiences, with no requirement to be a developer to ...
Resources
Featured
In this episode of Identiholics, host Christine Owen is joined by Jamie Danker from Venable and Carole House from Terranet. They discuss the importance of women in the cybersecurity field and the need for more women to be involved in privacy and security discussions. The conversation highlights the ...
The discourse around secure mobile communication platforms has escalated in the United States public sector, where security and data integrity aren’t just priorities but mandates. As agencies become increasingly dependent on digital technologies to execute their missions, the need for secure p...
Collibra has been named a Leader in The Forrester Wave™: Data Governance Solutions, Q3 2025 report, recognized for its strong vision and comprehensive capabilities. Download the report to explore emerging trends, evaluation criteria for governance tools, and why Collibra stands out in today&rs...
Ready to fast-track your implementation? The Road to Go-Live Handbook reveals proven strategies, expert tips, and step-by-step guidance to help you launch with confidence and deliver results faster. View this essential playbook for turning process insights into real business impact—download no...
Government agencies are facing increasing demands to provide services more efficiently, transparently, and with limited resources. To support this transformation, we're thrilled to share that Accela has acquired ePermitHub—marking a significant advancement in streamlining permitting and pl...

The Wiz + Accenture Responsive Protection System — a modern, unified cloud security platform tailored for federal agencies. A simple and secure way to enhance cloud security while reducing costs.

ActiveState’s Open Source Security Posture Management platform enables DevOps, InfoSec and Development teams to improve security status to deliver secure applications faster. Learn how ActiveState and Carahsoft have partnered up to provide comprehensive open-source management solutions in the ...
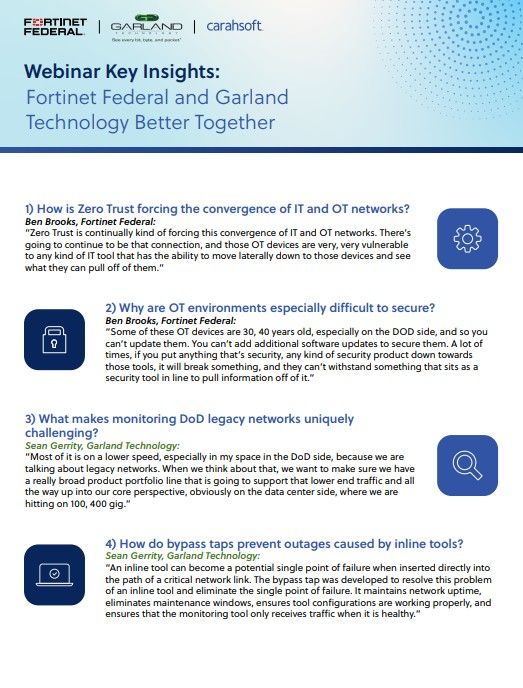
In the search for solutions to modernize legacy systems, federal agencies can consider integrations between Fortinet Federal and Garland Technology. Read highlights from the recent Better Together webinar with leading experts in IT and OT networks, Zero Trust architecture and federal ecosystems.
This resource provides an overview of EdgeRunner AI, a military-specific AI solution offering capabilities such as offline, multi-step, multi-turn interactions tailored for warfighters. It highlights features like EdgeRunner Athena for document summarization and domain-specific adapters with LoRA fi...
Access this Cohesity eBook to uncover six key predictions shaping the future of AI, data security, and cloud. As AI rapidly transforms industries, it brings both opportunities and risks—Cohesity experts provide actionable insights to help you stay ahead. Explore practical takeaways and valuabl...