Over the last several months, F5 has rolled out purpose-built AI assistants for F5 Distributed Cloud Services and F5 NGINX One. In February at AppWorld 2025 in Las Vegas, we also offered a preview of F5-powered AI assistant functionality specifically designed for F5 BIG-IP customers, centered on iRules code generation. Today, we’re thrilled to share two exciting milestones: we’re bringing together our AI assistants across the F5 Application Delivery and Security Platform, and availability of iRules code generation.
Managing application delivery and security often feels like solving a puzzle with missing pieces. From writing configurations to searching for answers in scattered documentation, these tasks consume time and energy while leaving teams vulnerable to errors and delays. Repetitive processes like debugging and policy tuning sap creativity, and even the most skilled teams inevitably encounter gaps in expertise that slow progress. These challenges are common, but they don’t have to define your workflows. With purpose-built AI-powered intelligence, teams can simplify these complexities with insights and automation designed to supercharge application delivery and security deployments.
Unification across the platform
To deliver exceptional customer experiences across the F5 Application Delivery and Security Platform, we are bringing our AI assistants into a single F5 AI Assistant. With a consistent user experience, SecOps and NetOps teams can better understand their security posture and exploit the wealth of information at their disposal across the entire platform, reducing the operational complexities of their hybrid multicloud environments.
F5 AI Assistant leverages the F5 AI Data Fabric to deliver intelligence powered by proprietary, purpose-built AI models. Unlike general AI tools, the AI Assistant provides domain-specific expertise, offering precise guidance and actionable insights. From generating iRules to optimizing configurations and improving security postures, it drives enterprise-grade accuracy and contextual relevance while reducing complexity. As part of the F5 Application Delivery and Security Platform, the AI Assistant empowers faster decision-making and measurable outcomes for teams managing modern application and security challenges.
iRules code generation is now available
F5 iRules are the backbone of customization within the BIG-IP ecosystem, empowering teams to tailor their application delivery and security environments to meet unique needs with unmatched precision and flexibility. Over 85% of BIG-IP customers rely on iRules, which power 70% of all BIG-IP instances globally. These dynamic scripts enable deep interaction with traffic, modifying behavior, optimizing routing, and solving challenges beyond standard configurations. However, iRules can be complex, time-intensive, and, in many cases, persist long after their authors have moved on from the company for which they were written. This level of control requires a tool that can match their importance, a tool designed to enhance their creation, use, and management for today’s scaling enterprises.
We’re excited to announce the availability of iRules code generation within the AI Assistant for our BIG-IP customers. This groundbreaking functionality leverages advanced automation with natural language processing, reshaping how teams build and manage iRules. With models trained using F5’s own expertise, including from our engineering and professional services teams, the AI Assistant simplifies the most complex aspects of iRules management by improving accuracy, reducing effort, and enabling faster security and application decisions. From streamlining workflows to eliminating manual processes, it empowers teams to achieve goals with efficiency, scalability, and innovation.
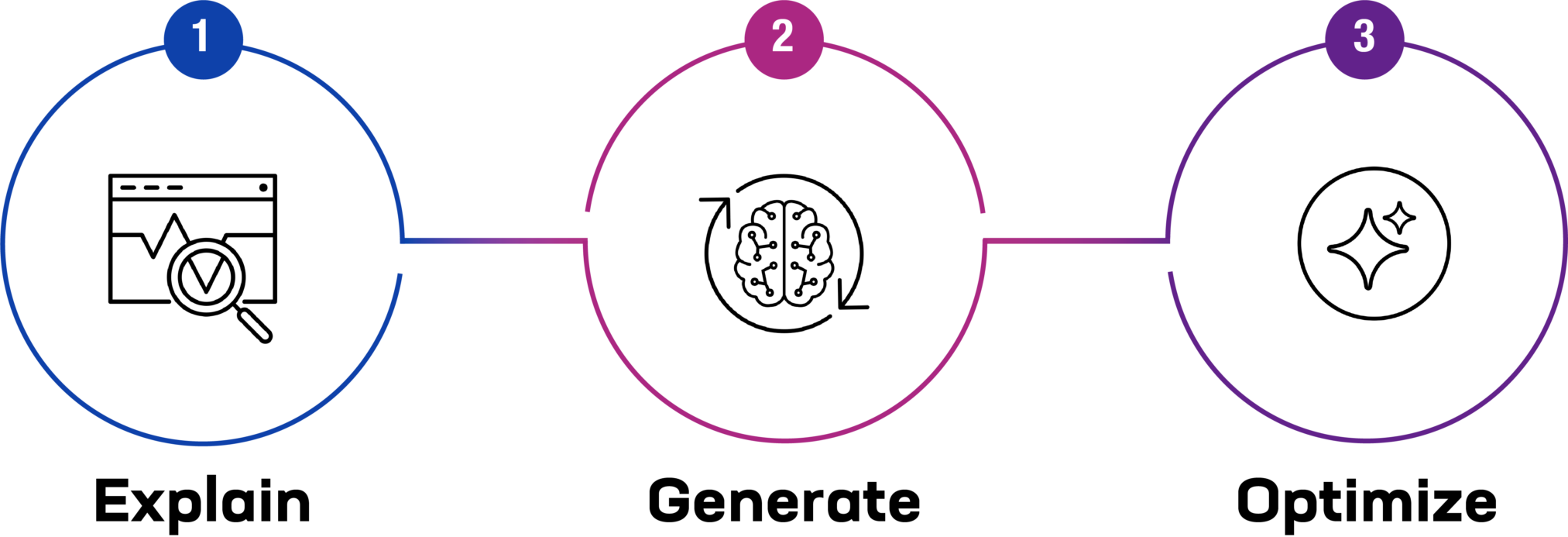
Functionality is categorized into three areas—explain, generate, and optimize:
- Explain: Gain a deeper understanding of iRules with clear, natural language explanations that break down components, logic, and functionality. This capability bridges knowledge gaps, making iRules accessible to users of all expertise levels while providing actionable insights for better decision-making.
- Generate: Instantly create secure, validated iRules by describing your needs in natural language. The AI Assistant translates your input into tailored scripts, saving valuable time, reducing errors, and accelerating deployments.
- Optimize: Debug, troubleshoot, and fine-tune iRules with precision and efficiency. The AI Assistant streamlines complex processes, eliminates manual guesswork, and ensures enhanced performance, reliability, and scalability for your BIG-IP environments.
The introduction of iRules code generation reinforces AI Assistant as your trusted partner for simplifying, innovating, and scaling BIG-IP environments. By eliminating guesswork, it ensures that teams can address vulnerabilities, maintain consistency, and manage traffic configurations swiftly and effectively.
Begin using F5 AI Assistant
To explore F5 AI Assistant for your organization, refer to our press release and the solution overview detailing iRules code generation and the strategic time-saving value the AI Assistant provides.
Also, be sure to catch all the latest F5 AI news on our Accelerate AI webpage.
Carahsoft Technology Corp. is The Trusted Government IT Solutions Provider, supporting Public Sector organizations across Federal, State and Local Government agencies and Education and Healthcare markets. As the Master Government Aggregator for our vendor partners, including F5 we deliver solutions for Geospatial, Cybersecurity, MultiCloud, DevSecOps, Artificial Intelligence, Customer Experience and Engagement, Open Source and more. Working with resellers, systems integrators and consultants, our sales and marketing teams provide industry leading IT products, services and training through hundreds of contract vehicles. Explore the Carahsoft Blog to learn more about the latest trends in Government technology markets and solutions, as well as Carahsoft’s ecosystem of partner thought-leaders.
This post originally appeared on F5.com, and is re-published with permission.