Federal missions operate across complex, distributed environments, from secure data centers to cloud enclaves and tactical platforms in disconnected conditions. Artificial intelligence (AI) must now match this operational agility.
Hybrid AI integrates cloud, on-premises and edge compute, enabling intelligence where and when it is needed. Whether inside a SCIF, within a FedRAMP-moderate enclave or in contested environments, hybrid architectures ensure trusted intelligence is continuously available to support mission outcomes.
Why Hybrid AI is Mission-Critical for Federal Agencies
As mission data becomes more dynamic and dispersed, centralized compute models alone cannot meet operational demands. Agencies must process, generate and act on information securely, whether in the field, across partner networks or in highly regulated environments.
Hybrid AI brings compute to the data, respecting governance and sovereignty while maintaining flexibility. AI capabilities must function reliably in environments where connectivity is degraded or unavailable, and where data cannot move freely due to classification or jurisdictional constraints.
This ensures real-time inference and decision support at the point of need while safeguarding CUI, PII and FOUO data under FISMA, EO 14110 and Zero Trust principles. AI-powered insights remain accessible even when the network does not.
The Technology Foundations of Mission-Ready Hybrid AI
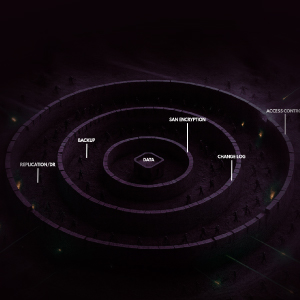
Data sovereignty is essential
Agencies must process, train and infer within regulatory boundaries, maintaining full control of sensitive data across its lifecycle, from edge ISR streams to classified model development. Containerized and optimized AI software must run flexibly across accelerated environments, from enterprise cloud to air-gapped data centers.
Infrastructure must scale seamlessly
Hybrid environments enable compute to move across core, cloud and field deployments, keeping AI aligned with changing mission needs.
Accelerated computing powers mission AI
Advanced generative and deep learning models demand high-efficiency, accelerated compute platforms. Hybrid AI leverages this capability to deliver high-throughput, low-latency insights not only in data centers but also at the tactical edge—essential for mission-aligned generative AI and emerging agentic applications.
Interoperability drives flexibility
Containerized AI microservices and API-driven architectures ensure seamless integration with mission platforms like health and geospatial, while enabling secure, policy-compliant operations across hybrid environments. Architectures should also support flexible integration of retrieval pipelines and evolving data governance models, ensuring mission intelligence is grounded in trusted, up-to-date sources.
Real-World Applications: Hybrid AI in Action
Agencies are applying hybrid AI today to extend mission capabilities beyond what centralized architectures allow.
In public health, sovereign data platforms combined with edge analytics support real-time outbreak modeling and informed containment planning. Disaster response teams ingest and analyze aerial imagery and IoT data locally, providing actionable insights even when disconnected from central networks.
Generative AI is transforming document-centric workflows. It accelerates the summarization of complex reports and regulatory analysis while maintaining strict control over sensitive content.
Sovereign AI innovation is advancing rapidly. National AI clusters allow agencies to train and refine models domestically, ensuring compliance with governance mandates while enhancing operational independence. Many of these efforts begin under SBIR, OTA or BPA contracts and evolve into modular architectures that scale with mission requirements.
Key Considerations for Building Hybrid AI

Hybrid AI success requires intentional architecture, policy fluency and alignment with mission realities.
Architectures must enable agility, supporting rapid adaptation to evolving mission needs, data sources and model advancements. Flexibility ensures AI remains relevant as both operational risks and opportunities evolve. Hybrid environments should also be designed to support emerging model types, including multi-modal, agentic and retrieval-augmented AI, and to accommodate evolving policy mandates.
Interoperability is essential. Open, standards-based pipelines and containerized services enable integration with evolving toolchains, partner ecosystems and commercial innovation while maintaining governance.
Federal leaders are using hybrid architectures to operationalize responsible AI principles outlined in EO 14110. Early alignment with procurement vehicles—OTAs, GWACs and BPAs—ensures scalable, policy-ready architectures. High-impact use cases, such as edge-deployed generative AI assistants and sovereign model training pipelines, continue to demonstrate the value of this approach.
Next Steps for Federal AI Leaders
Hybrid AI represents an inflection point for Federal missions. Leaders who invest in scalable, policy-aligned AI infrastructure today will be positioned to harness tomorrow’s AI innovations at mission speed.
By supporting secure, accelerated AI capabilities across edge, cloud and on-premises environments, hybrid architectures help agencies maintain operational advantage in any scenario. The focus is not just on deploying AI models, but on building adaptive infrastructure that delivers intelligence wherever the mission requires it.
Hybrid AI architectures also lay the operational foundation for the emerging era of AI Factories—systems that continuously generate, adapt and deploy intelligence at scale, across mission environments.
Federal leaders who establish this foundation today will ensure that AI serves the mission with the trust, agility and resilience it demands—and with the flexibility to evolve alongside the accelerating pace of innovation.