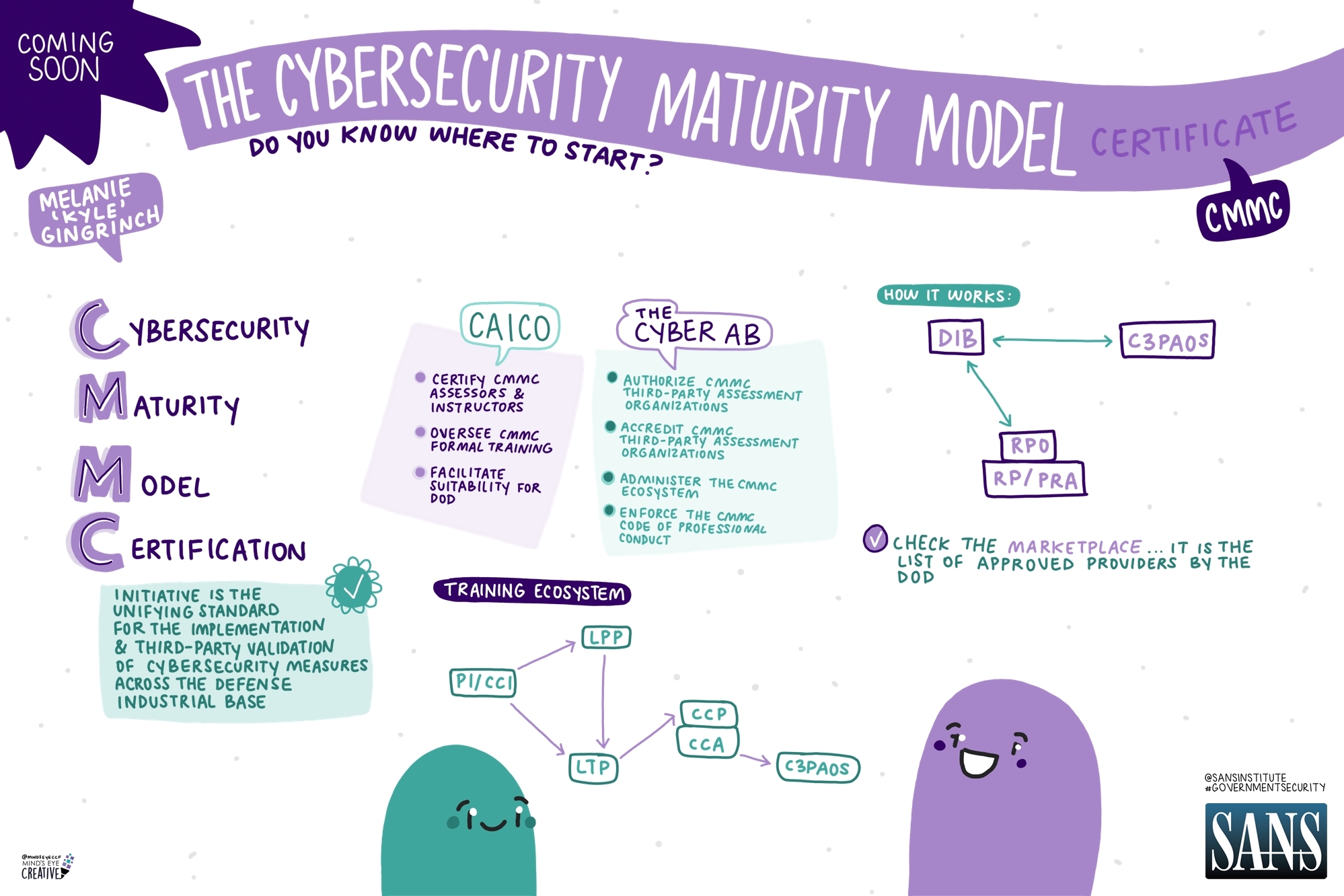
The Department of Defense (DoD) recently announced new cybersecurity compliance mandates for contractors and subcontractors in the DoD’s supply chain. Private companies that process, store or transmit DoD data are now required to comply with the Cybersecurity Maturity Model Certification, or CMMC.
The new mandate impacts every private company that handles Federal Contract Information (FCI) or Controlled Unclassified Information (CUI). That’s a large group: According to the DoD’s own estimation, at least 220,000 private companies currently have access to FCI and CUI and require CMMC certification.
Because the CMMC is relatively new, some organizations may be struggling to understand their obligations. Learn more about exactly what the CMMC is and what steps organizations should take right now to be prepared for audits and remain eligible for DoD contracts.
What Is CMMC?
CMMC is the cybersecurity compliance structure used by the Department of Defense. High-profile security breaches like Solar Winds highlighted the need for rigorous data protection throughout the DoD supply chain. The DoD implements the CMMC framework to vet potential contractors and subcontractors and protect against third-party data breaches.
There are three CMMC certification levels: 1, 2 and 3. The different levels correspond to the degree of sensitive information being handled. All companies that contract with DoD need to have at least Level 1 CMMC, while companies that handle more sensitive information will need to have Level 2 or Level 3 cybersecurity compliance certifications.
Recent Changes to CMMC
The CMMC has recently undergone some amendments. An older version of the CMMC, or CMMC 1.0, was implemented in 2019. The new version, CMMC 2.0, came into effect at the end of 2024.
Contractors must now comply with CMMC 2.0, although implementation is taking place in stages. For any organization contracting with the Defense Department, the most important takeaway is that you absolutely must be CMMC compliant to continue working with the Department.
What Level of CMMC Certification Do You Need?
If your organization handles any FCI or CUI, you’ll need CMMC certification. Which level is right for you? You can’t know for certain until you apply for a contract, as there is some variation from one external contract to another.
However, you can make an educated guess about the certification you’ll need. The DoD’s Scoping and Assessment Guide also provides more detail about the standards for each level.
Level 1 CMMC
Level 1 is the most straightforward CMMC certification. It doesn’t require third-party auditing; contractors do a self-assessment to get the certification.
Level 1 is usually appropriate for contractors who handle FCI material and nothing else. FCI is unclassified Government information that isn’t publicly available. Details about Government employees or facilities, for example, might be categorized as FCI. Although the information is sensitive, it is not considered critical enough to require the extra protection of a Level 2 or Level 3 certification.
Level 2 CMMC
If your organization handles both CUI and FCI, you will probably require Level 2 CMMC certification.
In many cases, Level 2 certification is straightforward and can be achieved through a self-certification process. However, in some cases you will need to pass a third-party audit for Level 2 certification. The procedure depends on the sensitivity of the data you’ll be handling. The more sensitive the information, the more precautions the DoD puts in place to prevent a potentially disastrous security breach.
Level 3 CMMC
Level 3 CMMC is the most serious and the most difficult certification to obtain. If your organization routinely handles both CUI and FCI and also deals with material that impacts DoD operations, then you may need this certification.
Level 3 CMMC mandates stricter protections than the other two certification levels. It’s required in cases where a data breach could create widespread problems for the Department of Defense, or even for national security.
To obtain Level 3 CMMC certification, you must undergo a Government audit. The Government will thoroughly assess your security system and determine whether it meets the appropriate standards for certification.
What Is the Cybersecurity Compliance Timeline?

CMMC 2.0 came into effect in December 2024. From that date on, organizations working with the Department of Defense are mandated to begin implementing CMMC compliance according to a 4-phase plan.
Phase 1
This stage began in December 2024, as soon as CMMC 2.0 came into effect. During Phase 1, prospective new DoD contractors are required to conduct a self-assessment to ensure cybersecurity compliance according to Level 1 or 2 CMMC. Phase 1 requirements went into effect November 10, 2025.
Phase 2
The full Level 2 standard comes into effect in November 2026, ushering in Phase 2 of CMMC 2.0. At this stage, contractors are subject to third-party audits to ensure cybersecurity compliance with Level 2 and Level 3 certification.
Phase 3
Phase 3 is set to begin in November 2027. At that time, organizations that handle the most sensitive data will be mandated to undergo a Government-run security audit to ensure compliance with Level 3 CMMC certification.
Phase 4
In November 2028, all new defense contracts will contain language stipulating the CMMC level requirement.
What Steps Should You Take To Comply with the CMMC?
Cybersecurity compliance is fairly straightforward and can be broken down into a few key steps.
Step One: Preparation
Determine which certification level is appropriate for your organization and its needs. Begin by deciding which contracts you’d like to apply for, and use the contracts to decide the appropriate certification level.
Remember that it’s always a good idea to aim for the lowest appropriate certification level, as higher levels are more difficult to obtain. If you are not dealing with highly sensitive data, it’s not worth trying to obtain the Level 3 certification.
Step Two: Internal Assessment
Conduct a preliminary assessment of your organization, analyzing where you will need to make changes to achieve cybersecurity compliance.
It’s good practice to do this in two stages. First, complete a self-assessment. Next, check your assessment with an objective source.
Step Three: Third-Party Audit
If you’re working towards Level 2 or Level 3 certification, you’ll need to be audited, either by an approved third-party auditor or by the Government. The CMMC marketplace makes it easy to set up the assessment. Again, you should first perform a self-assessment to make sure that you’ve addressed any shortfalls in your organization before you undergo this audit.
Step Four: Course Correction
The audit may reveal deficiencies in your security system. If so, you may be granted time to correct these deficiencies and still successfully apply for your CMMC certification.
Once you receive your CMMC certification, you’ll need to renew it once a year to confirm that your organization is keeping up with DoD best practices for cybersecurity.
Get Started With the CMMC Certification Process
- Get guidance on preparing for CMMC certification.
- Learn how one civil engineering firm worked with Onspring to earn its CMMC certification.
- Request a demo to explore the benefits of partnering with Onspring.