In today’s fast-paced digital world, security teams are under immense pressure to defend against a surge in sophisticated cyber threats. Expanding attack surfaces, driven by new technologies, cloud adoption, remote work and interconnected devices, create countless entry points for attackers. Security Operations Centers (SOCs) must evolve by leveraging automation, AI and machine learning (ML) to stay ahead—cutting through the noise, accelerating threat detection and streamlining responses to provide scalable, real-time defense against ever-evolving risks.
Modern SOC Challenges
As cyber threats continue to rise in both frequency and sophistication, SOCs are coping with an overwhelming volume of security incidents. Check Point Software’s 2025 Security Report reveals a staggering 44% year-over-year increase in cyberattacks, highlighting the urgent need for stronger, more scalable defenses.
Organizations are no longer operating within clearly defined perimeters. Today’s digital environments are sprawling and dynamic, spanning on-premises infrastructure, multi-cloud deployments, software as a service (SaaS) platforms, Internet of Things (IoT) devices and a remote workforce. Each layer adds complexity—and with it, new vulnerabilities. The expanding attack surface increases not only the number of potential entry points but also the volume of activity that must be monitored.
This leads to another major challenge: organizations are now generating unprecedented volumes of security data. SOCs are tasked with analyzing vast, continuous streams of telemetry to detect threats in real time but extracting meaningful insights from this flood of data has become increasingly difficult.
While traditional Security Information and Event Management (SIEM) systems remain a core component of enterprise security, they are struggling to keep up. Many SIEM platforms are constrained by schema designs, database capacity and a limit on the number of detection rules that can be ingested.
As a result, SOCs are often forced to make difficult trade-offs, choosing which data to collect and analyze based on storage and processing limitations. This selective approach creates blind spots, potentially allowing critical threats to go undetected. In fact, 56% of organizations report coverage gaps directly linked to the limitations of legacy SIEM systems, underscoring the need for modernization.
Alert fatigue is compounding the issue. Even well-configured SOCs can generate thousands of alerts daily, overwhelming analysts and increasing the risk of real threats being missed. According to a 2023 RSA survey by Gurucul, 61.37% of security teams report receiving more than 1,000 alerts per day, while 4.29% deal with over 100,000. Alarmingly, 19.74% say the volume is so high they cannot even quantify it.

Beyond the operational strain, cost is another major barrier. A medium-sized organization can produce terabytes of log data every day, and storing and processing this information—especially at the scale required for comprehensive threat detection—can cost hundreds of thousands annually. SOC leaders are under constant pressure to strike a balance between broad visibility and tight budget constraints.
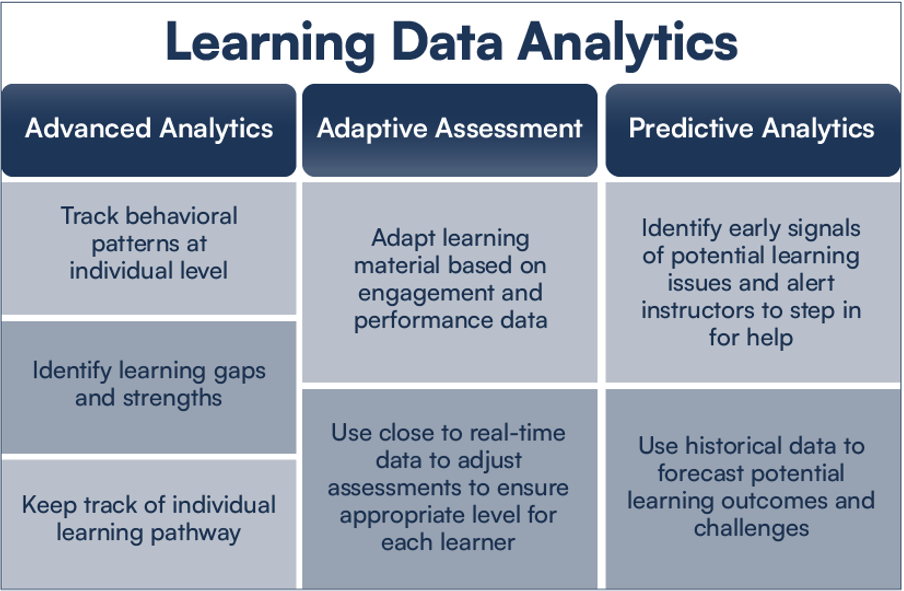
In this high-volume, high-velocity environment, traditional manual analysis simply cannot keep up. To close visibility gaps, reduce alert overload and operate efficiently at scale, organizations must adopt intelligent automation. Advanced analytics, ML and AI-driven detection can dramatically reduce noise, prioritize critical alerts and help SOC teams focus on what matters most—responding to real threats in real time.
The Role of Automation in SOC
Automation is a key force multiplier for SOC teams, enhancing threat response speed and accuracy. Over the past decade, security orchestration, automation and response (SOAR) solutions have had mixed success. While these solutions streamline workflows and incident response, they require significant maintenance, including scripting, playbook development and continuous security stack integration. The high total cost of ownership often outweighs initial investments, making long-term sustainability a challenge.
To address these limitations, SOCs are adopting telemetry pipelines, which intercept and filter traffic before SIEM processing, ensuring only relevant security data is analyzed. Advanced enrichment reduces redundant data, improving efficiency while lowering cloud storage costs.
Extended detection and response (XDR) solutions are also gaining traction. XDR integrates multiple security layers, correlates alerts locally and reduces reliance on centralized SIEMs. Vendor-specific XDR stacks work best within their own ecosystems but streamline threat detection and response.
Data lakes are becoming essential for long-term threat hunting, enabling analysts to detect subtle, prolonged attacks by retaining historical data for extended periods. This allows analysts to uncover patterns that might otherwise go unnoticed.
As SOC automation evolves toward autonomous SOC models and “SOCless” SIEM architectures, ML-driven algorithms will handle much of the processing and correlation, facilitating faster threat detection and response. By automating repetitive tasks like log analysis and low-level alert triage, SOC analysts can focus on complex investigations, enhancing security while addressing the skills gap.
Still, Gartner predicts that by 2030, 75% of SOC teams will see a decline in core security analysis skills as they grow too reliant on automation and AI. Therefore, deployments aimed at both augmenting human tasks and adding precision and speed to human investigations will be more effective than single-technique AI analytics. Striking the right balance between machine-driven speed and human insight seems like a feasible solution that keeps security teams agile, informed and in control of threats.
Evolving Technologies and Solutions
AI and ML capabilities enhance predictive analytics and threat-hunting capabilities, keeping SOC teams ahead of attackers. According to Gartner, by 2026, advancements like “action transformers” and the continued evolution of Generative AI (GenAI) will power semi-autonomous platforms that can greatly enhance and support the day-to-day operations of cybersecurity teams.
As cybersecurity AI assistants evolve, they will be used as more sophisticated tools for interactive support and investigation, covering tasks like incident response, risk assessment and code reviews. These tools are expected to boost efficiency and reduce response times, whether in organizations just building their security programs or in mature teams with established processes. These innovations improve threat detection and SOC readiness to withstand modern cyber risks.
Future SOC Operations
Progressive organizations understand the real value of AI/ML-powered SOC technologies that can be reasonably used and shift their focus from single-technique tools to building integrated systems that fuse software, AI and human expertise. Achieving scalable impact means having a clear strategy that targets the most meaningful opportunities.
Additionally, investment in workforce development and upskilling will be essential to bridging the cybersecurity talent gap. Organizations that invest in these areas will elevate their SOC effectiveness, better safeguard critical assets and build a resilient, future-ready cybersecurity posture.
To gain deeper insights into these strategies and hear directly from industry experts, watch SOC Prime’s webinar, “The SOC of the Future: Advanced Strategies to Evolve SOC for Modern-Day Enterprise Cybersecurity.”
Carahsoft Technology Corp. is The Trusted Government IT Solutions Provider, supporting Public Sector organizations across Federal, State and Local Government agencies and Education and Healthcare markets. As the Master Government Aggregator for our vendor partners, including SOC Prime we deliver solutions for Geospatial, Cybersecurity, MultiCloud, DevSecOps, Artificial Intelligence, Customer Experience and Engagement, Open Source and more. Working with resellers, systems integrators and consultants, our sales and marketing teams provide industry leading IT products, services and training through hundreds of contract vehicles. Explore the Carahsoft Blog to learn more about the latest trends in Government technology markets and solutions, as well as Carahsoft’s ecosystem of partner thought-leaders.