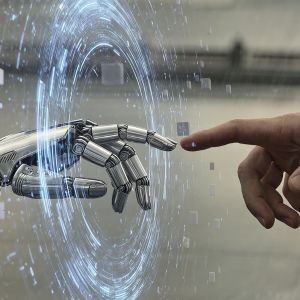
After 2020, the landscape of corporate real estate changed dramatically. Companies across multiple sectors, including technology, transitioned from working in office to either hybrid or totally remote models. Vacancy rates on corporate campuses increased to 15-20%, opening companies up to a multitude of liabilities and operational challenges. Artificial intelligence (AI) has brought a new edge to vacant building security. Smart guarding and solar guards elevate the security posture of vacant buildings, defend corporate assets and subsequently deliver a Return on Investment (ROI) through effective security measures.
Risks of Vacant Building Stewardship
Vacant buildings come with a series of unique risks to the company that either owns or leases the building. These locations are particularly attractive for criminal activity, especially trespassing and vandalism. Companies also face other risks such as copper theft and squatting that result in higher insurance claims, causing rising premiums. Further challenges come from the range in potential responses from law enforcement. The crime rate in the area will greatly affect how quickly police respond to the call, or whether they will respond at all if there is not an active incident.
Traditional security models for vacant buildings rely heavily on human patrols and come with their own operational drawbacks. A commonly used term in security, “warm bodyguards,” describes guards that are physically present but only do the bare minimum required to complete the job; in other words, these guards are just a warm body whose physical presence alone is deemed to be enough to deter criminal activity. Depending on the size and scope of the campus, these security measures can cost up to $25,000 per month. The ROI is negligible at best, and companies are often left with an expensive yet ineffective security protocol.
With property vacancy on the rise, companies need a solution that is cost effective but does not sacrifice protection or increase their risk profile. That solution lies in the integration of cutting-edge technology with human security.
The Modern Security Guard: Smart Guarding and Solar Guard
Prior to the existence of AI, the Silicon Valley Model sought to enhance building security by combining electronic access control in a building with a fleshed out in-person security protocol. This gives companies the opportunity to employ security guards with relevant prior experience, such as ex-law enforcement and ex-military members, who have effective communication and customer support skills. The key to success is a combination of the right people on site and the proper technological processes in place.
Sentry AI’s Smart Guarding takes this approach a step further by integrating AI agents into the security protocols. A various range of sensors are installed across the building. These can include:
- Cameras
- Microphones
- Motion sensors
- Turnstiles
- Fire detection (smoke detectors, heat detectors, etc.)
With the number of sensors that exist in a singular building, a Security Operations Center (SOC) analyst can get easily overwhelmed by the sheer volume of alerts. An AI agent established at the core of this alert system can absorb the information, interpret the incoming data and pass on the relevant security alerts to the SOC analysts.

The AI agent itself can also be proactive and mitigate ongoing security risks. The AI can impersonate a human guard, using any language, tone of voice or even slang if required. By voicing details such as the intruder’s clothing or appearance, the agent creates the impression of an on-site security guard without actually engaging physically with the intruder. After announcing a security presence, the agent will tell the intruder to leave and threaten police intervention if they do not. The agent can also activate sirens and lights to trigger a flight response from the intruder. This is all managed without human intervention.
Periodically, companies need to install a security solution that does not rely on the network, property owner or landlord. Sentry AI has the Solar Guard solution for these exact situations. The Solar Guard is a self-contained mobile unit with a tall mast and several solar panels. Energy collected throughout the day is stored in batteries contained within the unit to power it throughout the night or in adverse weather conditions. At the top of the mast, the Solar Guard has lights, speakers, a cellular modem and dual lens cameras that give a 360-degree field of vision.
As vacancy rates in corporate buildings continue to climb, companies continue to search for new impactful and cost-effective ways to improve their security posture in their buildings. AI-powered security protocols such as Solar Guard and Smart Guarding decrease the risk to personnel and cut through alert fatigue. By combining modern technological advancements with knowledgeable SOC analysts, companies gain ROI and protect their assets when personnel are not present.
To discover how Smart Guarding can elevate security in your vacant facilities, watch Sentry AI’s webinar, “Using AI to Protect Vacant Facilities.”
Carahsoft Technology Corp. is The Trusted Government IT Solutions Provider, supporting Public Sector organizations across Federal, State and Local Government agencies and Education and Healthcare markets. As the Master Government Aggregator for our vendor partners, including Sentry AI, we deliver solutions for Geospatial, Cybersecurity, MultiCloud, DevSecOps, Artificial Intelligence, Customer Experience and Engagement, Open Source and more. Working with resellers, systems integrators and consultants, our sales and marketing teams provide industry leading IT products, services and training through hundreds of contract vehicles. Explore the Carahsoft Blog to learn more about the latest trends in Government technology markets and solutions, as well as Carahsoft’s ecosystem of partner thought-leaders.