Process-Oriented OT Cybersecurity with SIGA
Federal agencies and regulated operators of critical infrastructure are entering a new phase in operational technology (OT) cybersecurity. While many sectors have long followed voluntary guidance such as the National Institute of Standards and Technology (NIST) Special Publication (SP) 800-82 Revision 3, recent years have seen a steady tightening of Federal cyber incident reporting requirements for critical infrastructure. This trend continues in 2025 with additional sector-specific rules taking effect and the Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) moving toward its final rule.
From Guidance to Requirements
Federal oversight of OT cybersecurity has moved beyond broad guidelines into a phase where specific reporting obligations are being set by sector. The shift reflects a growing emphasis on timely and consistent incident data that can be used for coordinated national response.
In 2025, several key developments are shaping the landscape:

- Pipelines: The Transportation Security Administration (TSA) Security Directive Pipeline-2021-02F, effective May 3, 2025, continues to require mitigation measures, testing and contingency planning for pipeline operators. These measures have been in place since the Colonial Pipeline incident and are now firmly embedded in regulatory practice.
- Water and Wastewater: The EPA Water Sector Cybersecurity Program has updated its technical assistance and incident-response guidance. While participation is voluntary, the program mirrors many of the practices found in regulated sectors, indicating where expectations are headed.
- CIRCIA: The Act is expected to be finalized in late 2025. Once in effect, it will require reporting significant incidents within 72 hours and ransomware payments within 24 hours, creating a cross-sector Federal baseline for incident reporting.
For Public Sector operators in energy, transportation, water and other essential services, these actions confirm that Federal expectations are moving toward consistent, evidence-based incident reporting across critical infrastructure.
The Reporting Challenge in OT Environments
Meeting Federal reporting requirements depends not only on having the right policies in place but also on the ability to detect and verify incidents quickly. In OT environments, many cyber events start as small changes in process behavior that do not appear in traditional network monitoring. When these early signs go unnoticed, agencies may be unable to confirm the incident, assess its impact or provide the detailed operational evidence that regulators require.
In the Purdue Enterprise Reference Architecture (commonly referred to as the Purdue Model), Level Zero refers to the lowest layer of an industrial control system. This is where raw input and output (I/O) signals from field devices report the actual status of equipment such as pumps, valves, circuit breakers and turbines. These electrical signals are the first and most reliable indicators of what is happening in a physical process, and they exist independently of the network data that higher levels use.
Without visibility into Level Zero, operators face several obstacles:
- Difficulty confirming whether a cyber event has actually affected operations
- Limited ability to quantify operational and safety impacts with precision
- Gaps in the time-stamped evidence needed to meet short Federal reporting windows
The challenge is heightened in environments that mix aging legacy systems with modernized control platforms. These environments often lack unified monitoring, making it harder to capture the unaltered operational data regulators now expect.
Why Process-Oriented OT Cybersecurity Matters
In the Purdue Model, Level Zero is the process interface where the control system reads and drives raw I/O signals. Those unprocessed signals provide the closest, most reliable view of real operating conditions, so early signs of a cyber-physical impact frequently show up there first.
Process-oriented OT cybersecurity focuses on monitoring these raw signals in real time. By capturing them out of band from the operational network, agencies gain a trusted source of truth that cannot be spoofed or altered by a network-based attack. This data enables:
- Clear timelines of operational changes before, during and after an incident
- Early detection of anomalies that may indicate tampering or failure
- Reliable forensic evidence for post-incident reporting and compliance audits
This approach bridges the gap between traditional IT security tools and the operational realities of critical infrastructure, ensuring that reporting requirements can be met with both speed and accuracy.
SIGA’s Role in Compliance Readiness
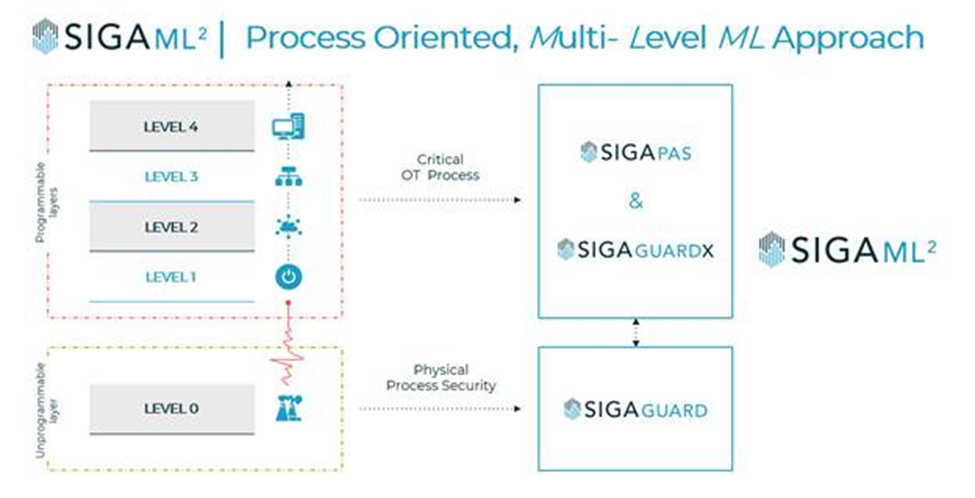
SIGA delivers process-oriented OT cybersecurity for critical infrastructure. SigaGuard connects directly to control-system I/O modules and continuously monitors raw electrical signals at Level 0, entirely out of band from the operational network. This preserves system performance and provides a tamper-proof view of operational data.
SigaGuardX: Early Threat Detection
SigaGuardX supports evidence-based determination of when a cyber event is underway. It classifies whether activity reflects normal operations or an OT cyber breach by applying multiple artificial intelligence (AI) models and cross-referencing the MITRE database of known attacks. It also performs real-time comparisons between Level 0 signal behavior and data from Levels 1 through 4 to surface possible false-data injection attacks, including Stuxnet-like patterns.
Siga-PAS: Process Attack Simulation
Software-based simulated anomalies replicate real-world attack scenarios. Siga-PAS enables agencies to prepare for and respond to OT-specific threats without disrupting ongoing operations, while validating detection logic, incident playbooks and reporting workflows.
Compliance Outcomes
- High-fidelity operational evidence that aligns with CIRCIA and sector-specific reporting requirements
- Regulator-ready forensic records of sequence, scope and impact
- Faster reporting through actionable alerts with operational context
- Rapid verification of whether a cyber event affected critical processes
By integrating SIGA’s Level 0 monitoring into existing security operations, agencies can meet tightening Federal reporting requirements and improve their ability to detect, contain and recover from OT cyber incidents. This strengthens both regulatory compliance and the continuity of essential public services.
Visit Carahsoft’s SIGA solutions page to learn more about how SIGA’s cyber-physical security solutions can strengthen your agency’s infrastructure.
Carahsoft Technology Corp. is The Trusted Government IT Solutions Provider, supporting Public Sector organizations across Federal, State and Local Government agencies and Education and Healthcare markets. As the Master Government Aggregator for our vendor partners, including SIGA, we deliver solutions for Geospatial, Cybersecurity, MultiCloud, DevSecOps, Artificial Intelligence, Customer Experience and Engagement, Open Source and more. Working with resellers, systems integrators and consultants, our sales and marketing teams provide industry leading IT products, services and training through hundreds of contract vehicles. Explore the Carahsoft Blog to learn more about the latest trends in Government technology markets and solutions, as well as Carahsoft’s ecosystem of partner thought-leaders.


 Realities of Critical Infrastructure Environments
Realities of Critical Infrastructure Environments