When a cyber incident occurs in an operational technology (OT) environment, understanding what is actually happening can become difficult. Control systems may continue to display normal readings even if attackers have begun manipulating logic or feedback within Programmable Logic Controllers (PLCs) or Human-Machine Interfaces (HMIs). Operators see stable values while underlying conditions start to diverge from what is shown on screen.
If process data at the controller level is falsified, every connected monitoring and cybersecurity tool reflects the same false picture. At that point, the Chief Information Security Officer (CISO) and operations team lose reliable visibility into the physical process that underpins production and safety.
The choices that follow each carry risk:
- Shutting down operations may prevent escalation but could also cause costly downtime if the intrusion is contained to the network.
- Continuing to operate may expose critical assets to damage if the manipulation extends to the process layer.
A recent cyber event at Norway’s Risevatnet dam illustrates this limitation.
During the incident, operators lost visibility into parts of the control system, yet intrusion detection and monitoring tools reported no anomalies. The breach was discovered only when on-site personnel noticed irregular behavior in equipment operations.

This outcome speaks to a broader issue in OT cybersecurity. Network-based detection tools can confirm whether communication channels are functioning, but they cannot independently verify whether the process data itself is genuine. If attackers manipulate information within PLCs or HMIs, every connected dashboard, alarm and analytic layer reflects the same falsified values. In effect, the system becomes blind at the moment visibility is most needed.
The Risevatnet case shows how quickly a cybersecurity failure can become an operational one. When control room data appears normal, incident response slows and decisions depend on incomplete or misleading information. Without a way to validate what is happening at the physical process level, teams must rely on manual observation or external cues, a reactive approach that offers no real protection in complex or distributed environments.
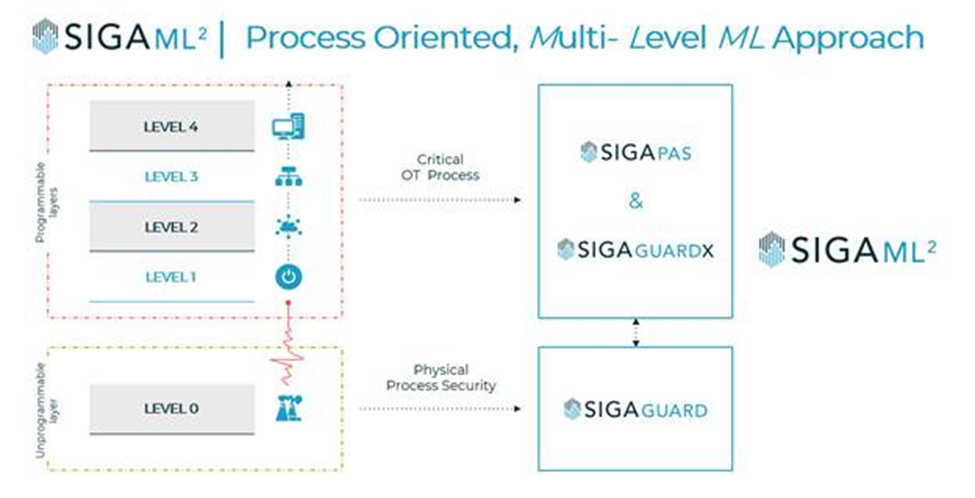
SIGA’s SigaML², available through Carahsoft, addresses this visibility gap by providing an independent, out-of-band view of the industrial process. The system collects unfiltered electrical signals directly from field I/Os (data that cannot be spoofed or altered) and applies multi-level analytics across Purdue Levels 0–4 to detect anomalies and false-data injections in real time.
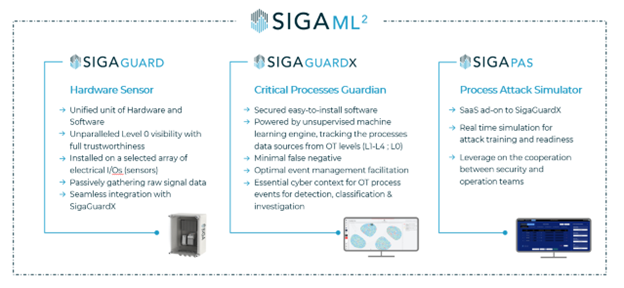
Its components work together to create an evidence-based view of the process:
- SigaGuard sensors capture raw electrical data directly from equipment.
- SigaGuardX software correlates Level 0-4 information to identify inconsistencies and possible manipulations.
- S-PAS simulation tools allow cybersecurity and operations teams to rehearse attack scenarios and refine incident response playbooks.
These capabilities give CISOs and plant operators verifiable insight during an active incident, helping determine whether an event is operational or cyber in nature and guiding containment or recovery actions.
Regulatory frameworks including Network and Information Security Directive 2 (NIS2), Cyber Incident Reporting for Critical Infrastructure Act (CIRCIA) and the latest National Institute of Standards and Technology (NIST) guidance highlight the importance of process-level monitoring and validation.
As oversight expands, CISOs and plant operators are expected to provide verifiable evidence of what occurred during an event, more than network logs or alarms.
Meeting that requirement depends on having data sources that remain trustworthy even when control networks are compromised.
SigaML² provides that capability, giving security and operations teams a direct, unaltered view of the physical process when clarity matters most.
Explore how SIGA’s cyber-physical security solutions empower CISOs with greater visibility during OT attacks. Visit Carahsoft’s SIGA solutions page to discover how your agency can enhance its infrastructure resilience.
Carahsoft Technology Corp. is The Trusted Government IT Solutions Provider, supporting Public Sector organizations across Federal, State and Local Government agencies and Education and Healthcare markets. As the Master Government Aggregator for our vendor partners, including SIGA, we deliver solutions for Geospatial, Cybersecurity, MultiCloud, DevSecOps, Artificial Intelligence, Customer Experience and Engagement, Open Source and more. Working with resellers, systems integrators and consultants, our sales and marketing teams provide industry leading IT products, services and training through hundreds of contract vehicles. Explore the Carahsoft Blog to learn more about the latest trends in Government technology markets and solutions, as well as Carahsoft’s ecosystem of partner thought-leaders.