Open source technology accounts for a significant portion of most modern applications, with some estimates going as high as 90%, and it is the foundation of many mainstream technologies. Its strength lies in the fact that a vibrant ecosystem of developers contribute to and continually improve the underlying code, which keeps the software dynamic and responsive to changing needs. Enterprise open source software further augments these community-driven projects by providing enterprise-grade support and scalability, while retaining the innovation and flexibility driven by the open source development model. By providing the best of both worlds, such solutions represent a powerful arsenal of tools for addressing government’s most pressing challenges. In a recent pulse survey of FCW readers, 93% of respondents said they were using open source technology. And more than half of respondents to FCW’s survey see open source as an integral resource for strengthening cybersecurity. That number reflects a positive trend toward a better understanding of open source software’s intrinsic approach to security. The power of enterprise open source technologies lies in a combination of collaboration, transparency and industry expertise. As agencies expand their use of such technologies, they maximize their ability to achieve mission success in the most secure, agile and innovative way possible. Learn how the combined power of community-driven innovation and industry-leading technical support is expanding the government’s capacity for transformation in Carahsoft’s Innovation in Government® report.
Why Open Source is a Mission-Critical Foundation
 “Open source transforms the way agencies manage hybrid and multi-cloud environments. The most critical technology in the cloud, across all providers, is Linux. Everything is built on top of that foundation — both the infrastructure of the cloud and cloud offerings. Given the right partner, the promise of Linux is that it provides a consistent technology layer for agencies across all footprints, including multiple cloud providers, on-premises data centers and edge environments. From that foundation, agencies and their partners can build portable architectures that leverage other open source technologies. Portability gives organizations the ability to use the same architectures, underlying technologies, monitoring and security solutions, and human skills to manage mission-critical capabilities across all footprints.”
“Open source transforms the way agencies manage hybrid and multi-cloud environments. The most critical technology in the cloud, across all providers, is Linux. Everything is built on top of that foundation — both the infrastructure of the cloud and cloud offerings. Given the right partner, the promise of Linux is that it provides a consistent technology layer for agencies across all footprints, including multiple cloud providers, on-premises data centers and edge environments. From that foundation, agencies and their partners can build portable architectures that leverage other open source technologies. Portability gives organizations the ability to use the same architectures, underlying technologies, monitoring and security solutions, and human skills to manage mission-critical capabilities across all footprints.”
Read more insights from Christopher Smith, Vice President and General Manager of the North America Public Sector at Red Hat.
How Open Source is Expanding its Mission Reach
“The real power of open source technologies was revealed when they cracked the code on being highly powered, mission-specific, distributed systems. That’s how we are able to get insights out of data by being able to hold it and query it. Today, open source innovation is being accelerated by the cloud, and the conversation is still changing, with people now demanding that their open source companies be cloud-first platforms. Along the way, the open source technologies that start in the community and then receive a boost of commercial innovation have matured. The most powerful ones are expanding their ability to address more of the government’s mission needs. They are staying interoperable and keeping the data interchange non-proprietary, which is important for government agencies.”
Read more insights from David Erickson, Senior Director of Solutions Architecture at Elastic.
The Open Source Community’s Commitment to Security
“A central tenet of software development is visibility and traceability from start to finish so that a developer can follow the code through development, testing, building and security compliance, and then into the final production environment. Along the way, there are some key activities that boost collaboration and positive outcomes, starting with early code previews, where developers can spin up an application for stakeholders to review. Other activities include documented code reviews by peers to ensure the code is well written and efficient. In addition, DevOps components such as open source, infrastructure as code, Kubernetes as a deployment mechanism, automated testing, and better platforms and capabilities have helped developers move away from building ecosystems and instead focus on innovation.”
Read more insights from Joel Krooswyk, Federal CTO at GitLab.
The Limitless Potential of an Open Source Database
“One of the most important elements of any database migration is ensuring that proper planning and due diligence have been performed to ensure a smooth and successful deployment. In addition, there are some key considerations agencies should keep in mind when moving to open source databases. It is essential to start with a clear understanding of the business case and objectives for adopting an open source approach. Agencies also need to decide how the database should function and what it should do to support their digital transformation. Then they must choose the optimal method to deploy the database.”
Read more insights from Jeremy A. Wilson, CTO of the North America Public Sector at EDB.
Modernizing Digital Services with Open Source
“A composable, open source digital experience platform (DXP) enables agencies to overcome those challenges. Open source technology is continuously contributed to by a community of developers to reflect a wide array of needs across organizations in varying industries and of varying sizes. A composable approach allows agencies to assemble a number of solutions for a fast, efficient system that is tailored to their needs. When agencies combine a composable DXP with open source technology, they have access to best-of-breed software and the ability to customize the assembly to suit their requirements. An enterprise DXP will enable agencies to achieve a 360-degree view of how constituents are engaging with their digital services and gain valuable data to understand how to enhance their experience. Finally, a composable, open source DXP provides a proactive approach to protecting against security and compliance vulnerabilities.”
Read more insights from Tami Pearlstein, Senior Product Marketing Manager at Acquia.
Creating Secure Open Source Repositories
“Protecting the software supply chain requires looking at every single thing that might come into an agency’s environment. To understand that level of visibility, I like to use the analogy of a refrigerator. All the ingredients necessary to make a cake or pie are in the refrigerator. We know they are of good quality, and other teams can use them instead of having to find their own. At Sonatype, our software equivalent of a refrigerator is the Nexus Repository Manager. A second aspect of our offering, called Lifecycle, allows us to evaluate the open source components in repositories at every stage of the software development life cycle. One piece of software can download a thousand other components. How do we know if one of those components is malicious?”
Read more insights from Maury Cupitt, Regional Vice President of Sales Engineering at Sonatype.
Better Data Flows for a Better Customer Experience
“A more responsive and personalized customer experience isn’t much different from the initial problem set that gave birth to Apache Kafka. When people interact with agencies, they want those agencies to know who they are and how they’ve interacted in the past. They don’t want to be asked for their Social Security number three times on the same phone call. They also expect that the information or service they receive will be the same whether they are accessing it over the phone, via a mobile app and on a website. To elevate the quality of their service, agencies must be able to stream information in a low-friction way so different systems are consistent with one another and up-to-date at all times, regardless of the communication channel an individual uses. President Joe Biden’s executive order about transforming the federal customer experience is based on this capability. The most successful companies across industries have figured out how to do it, and for the most part, they’ve done it with open source software.”
Read more insights from Jason Schick, General Manager of Confluent US Public Sector.
An Open Source Approach to Data Analytics
“For the past 40 years, agencies have used data warehouses to collect and analyze their data. Although those warehouses worked well, they were limited in what they could do. For instance, they could only handle structured data, but by some estimates, 90% of agencies’ data is unstructured and in the form of text, images, audio, video and the like. Furthermore, proprietary data warehouses can show agencies what has happened in the past but can’t predict what might happen in the future. To achieve the government’s goal of evidence-based decision-making, agencies need to be able to tap into all their data and predict what might come next.”
Read more insights from Howard Levenson, Regional Vice President at Databricks.
Download the full Innovation in Government® report for more insights from these open source thought leaders and additional industry research from FCW.

 Robust Cybersecurity on a Budget
Robust Cybersecurity on a Budget For
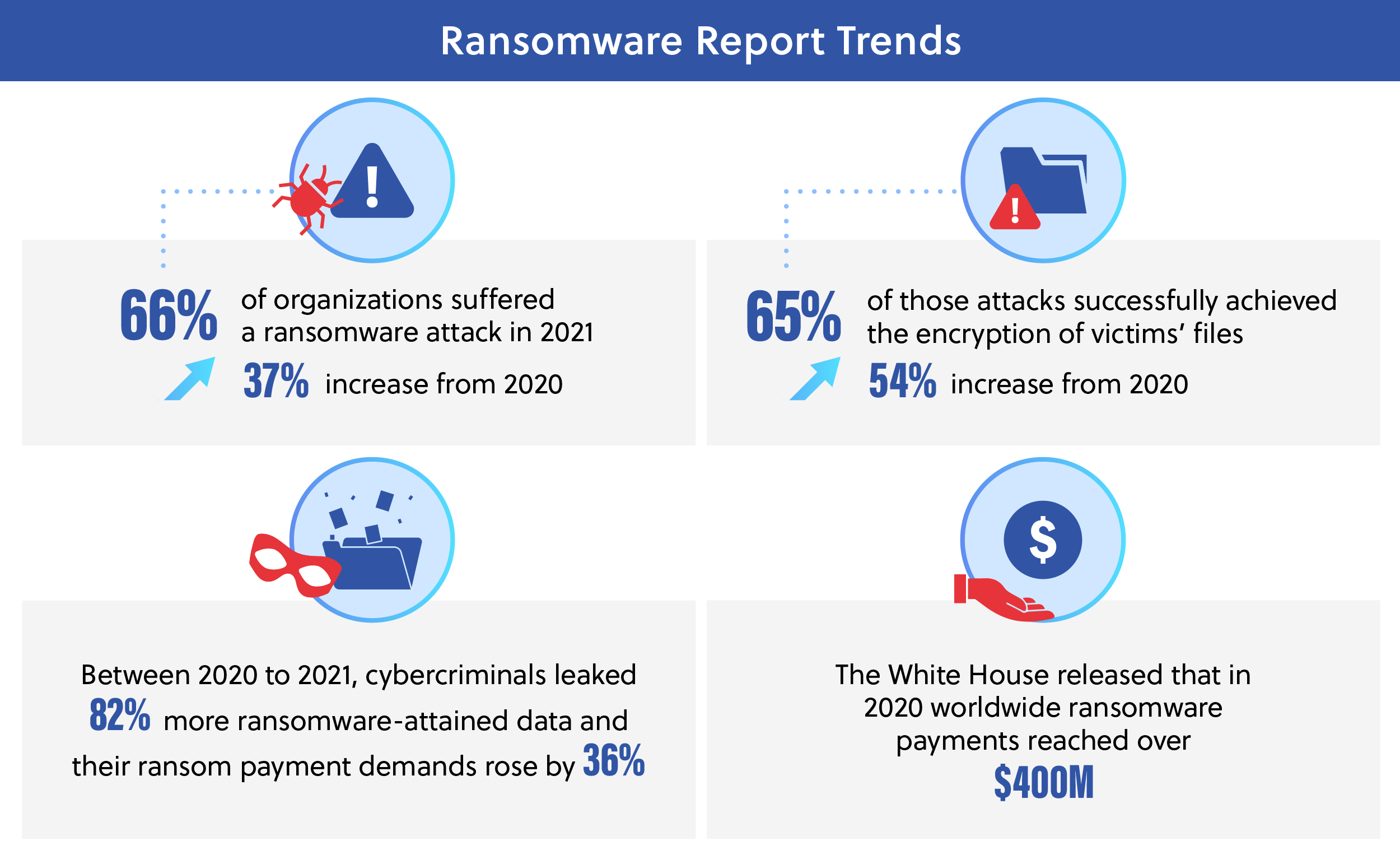
For  Ransomware is a form of extortion through malware exploiting cyber vulnerabilities to infiltrate systems and capture vital operating or private data. The cybercriminals require payment, often in the form of cryptocurrency, for the release, restoration or decryption of the files or the assurance of not blackmailing individuals with the information accessed. Only 2% of organizations within healthcare get their full data back even after paying the ransom, with the majority of organizations receiving about 65% of their information back.[
Ransomware is a form of extortion through malware exploiting cyber vulnerabilities to infiltrate systems and capture vital operating or private data. The cybercriminals require payment, often in the form of cryptocurrency, for the release, restoration or decryption of the files or the assurance of not blackmailing individuals with the information accessed. Only 2% of organizations within healthcare get their full data back even after paying the ransom, with the majority of organizations receiving about 65% of their information back.[