In July 2021, the presidential administration signed a National Security Memorandum on Improving Cybersecurity for Critical Infrastructure Control Systems. As these systems are a part of daily life, any damage to them would be a significant threat to national security. One major part of critical infrastructures, the Water and Wastewater Systems Sector, plays a vital part in daily life.
The first part of this four-part blog series covered the basics of critical infrastructure cybersecurity. This is the second part, and subsequent blogs will dive deeper into the electric, utility and transportation sectors respectively.
 The Water and Wastewater Sector in the United States
The Water and Wastewater Sector in the United States
The Water and Wastewater Systems Sector is a critical infrastructure sector focused on water and wastewater sources and the protection of such sources.
This sector is one of the United States’ critical infrastructures: a physical and/or cyber asset that is so vital that their destruction would have a debilitating effect on society, whether physical, economic or safety related. While the water and wastewater industry is vulnerable to physical attacks it is also in jeopardy to cybersecurity attacks, as the sector increasingly relies on internet of things devices, automation, sensors, data collection, network devices and analytics software.[1] Recent water infrastructure attacks, such as the login breach that affected water treatment programs in the San Francisco Bay Area, or the breach to the industrial control systems (ICS) in Oldsmar, Florida, demonstrated how easy it was for foreign threats to not only hack critical infrastructure, but to shake the public’s confidence. While Industrial Control Systems owners and operators manage their own security, federal agencies seek to protect ICS technologies from potential exploitations that pose existential threats to the public or US property.
The Initiative to Improve Cybersecurity for Critical Infrastructure
To combat potential threats, the White House has put forth the National Security Memorandum on Improving Cybersecurity for Critical Infrastructure Control Systems, an initiative that aims to safeguard the critical infrastructure of the Nation. The memorandum mentions the Water and Wastewater Systems sector by name in section 3a, spearheading the path for the government to act against threats. By working directly with critical infrastructure stakeholders, owners and operators, the White House will establish baseline cybersecurity goals and technology that facilitate threat visibility and detection so that the government and respective industry may take immediate action against any breaches.[1]
The EPA Initiative
As a part of the National Security Memorandum, the Environmental Protection Agency (EPA), a federal agency in charge of risk management for environmental health, announced the Industrial Control Systems Cybersecurity Initiative – Water and Wastewater Sector Action Plan to join in protecting water systems from cyberattacks. This 2022 plan focuses on supporting the early detection and expulsion of cyber threats against the water sector. A few of its action points include:
- Creating a task force of water sector leaders
- Adding new projects that demonstrate and implement the adoption of incident monitoring
- Improving the process of information sharing and data analysis
- Providing technical support to water systems[2]
With this properly implemented, the Water and Wastewater Systems sector can survive a cyber-event with no loss of critical function. The Cybersecurity and Infrastructure Security Agency (CISA) cybersecurity performance goals, a set of voluntary goals released in accordance with the National Security Memorandum, are broadly applicable to critical infrastructure sectors, including the water and wastewater sector. Industries can utilize these collaborative cybersecurity government resources to improve their safety.
A Unified Initiative
As the world becomes increasingly more interconnected with networks and the internet, cybersecurity grows in importance. To protect one of the most vital US infrastructures, water and waste, federal agencies have come together to with initiatives to encourage agencies to implement strong security practices to protect US environments and the public.
Check out the first part of our series on cybersecurity infrastructure. The third installment of this series will cover best cybersecurity practices in the electric utility sector.
To learn more about how agencies can bolster their cybersecurity efforts within critical infrastructure, visit Carahsoft’s Cybersecurity Solutions Portfolio.
Resources:
[1] “National Security Memorandum on Improving Cybersecurity for Critical Infrastructure Control Systems,” The White House, https://www.whitehouse.gov/briefing-room/statements-releases/2021/07/28/national-security-memorandum-on-improving-cybersecurity-for-critical-infrastructure-control-systems/
[2] “EPA Announces Action Plan to Accelerate Cyber-Resilience for the Water Sector,” United States Environmental Protection Agency, https://www.epa.gov/newsreleases/epa-announces-action-plan-accelerate-cyber-resilience-water-sector

 Realities of Critical Infrastructure Environments
Realities of Critical Infrastructure Environments
 Strong, resilient next-generation networks that protect sensitive data and DoD missions and functions have never been more critical. But, with a complex interconnected information environment, how can federal IT teams strengthen cybersecurity and become proactive instead of reactive? Army leaders have spent much time discussing resilient next-generation networking, but action needs to be taken soon.
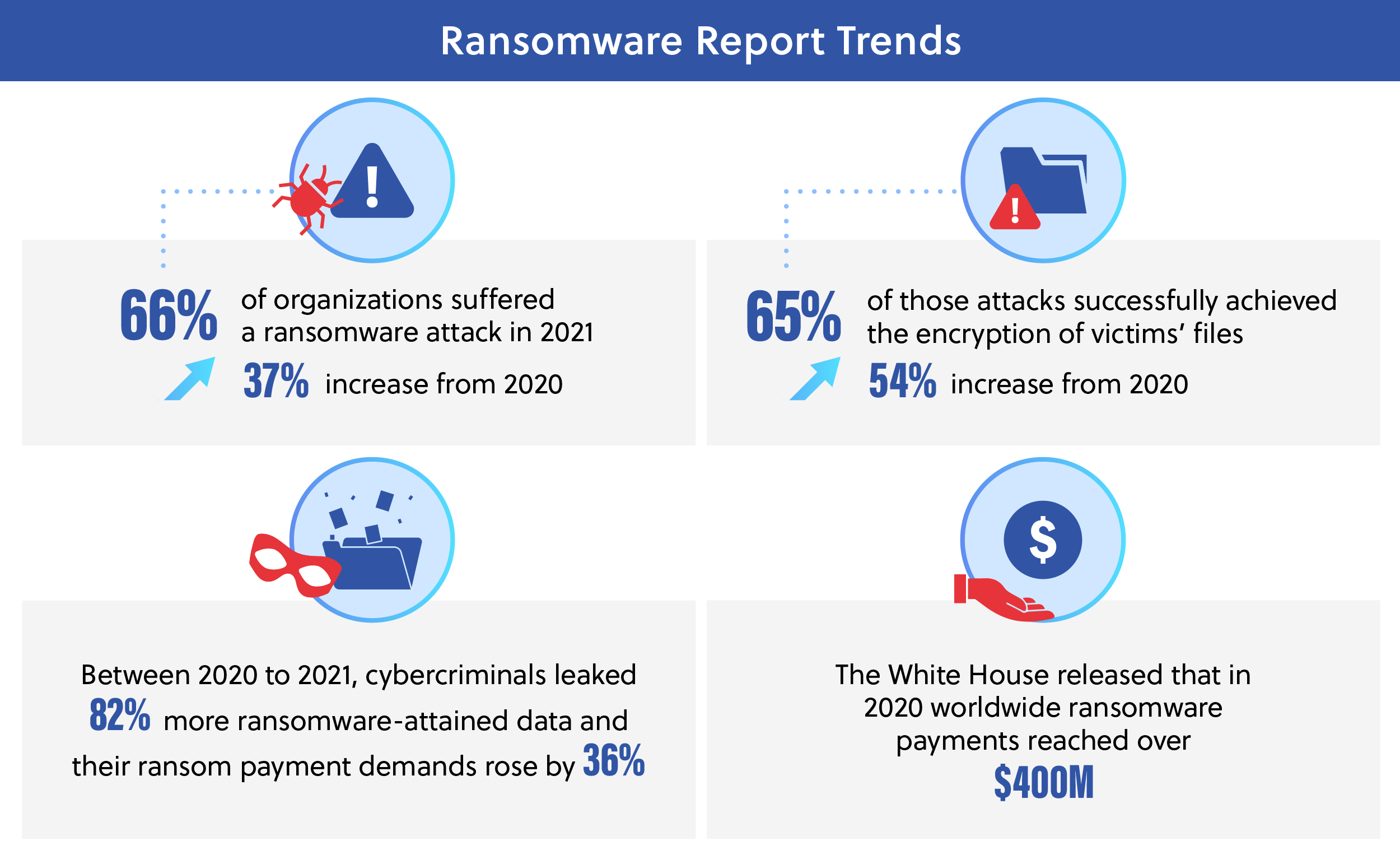
Strong, resilient next-generation networks that protect sensitive data and DoD missions and functions have never been more critical. But, with a complex interconnected information environment, how can federal IT teams strengthen cybersecurity and become proactive instead of reactive? Army leaders have spent much time discussing resilient next-generation networking, but action needs to be taken soon. Ransomware is a form of extortion through malware exploiting cyber vulnerabilities to infiltrate systems and capture vital operating or private data. The cybercriminals require payment, often in the form of cryptocurrency, for the release, restoration or decryption of the files or the assurance of not blackmailing individuals with the information accessed. Only 2% of organizations within healthcare get their full data back even after paying the ransom, with the majority of organizations receiving about 65% of their information back.[
Ransomware is a form of extortion through malware exploiting cyber vulnerabilities to infiltrate systems and capture vital operating or private data. The cybercriminals require payment, often in the form of cryptocurrency, for the release, restoration or decryption of the files or the assurance of not blackmailing individuals with the information accessed. Only 2% of organizations within healthcare get their full data back even after paying the ransom, with the majority of organizations receiving about 65% of their information back.[