Latest in Technology and Government
-
The Top 5 Insights for Government from HIMSS 2026
At HIMSS 2026, healthcare leaders shared five key insights driving interoperability, data modernization and a more connected health system.
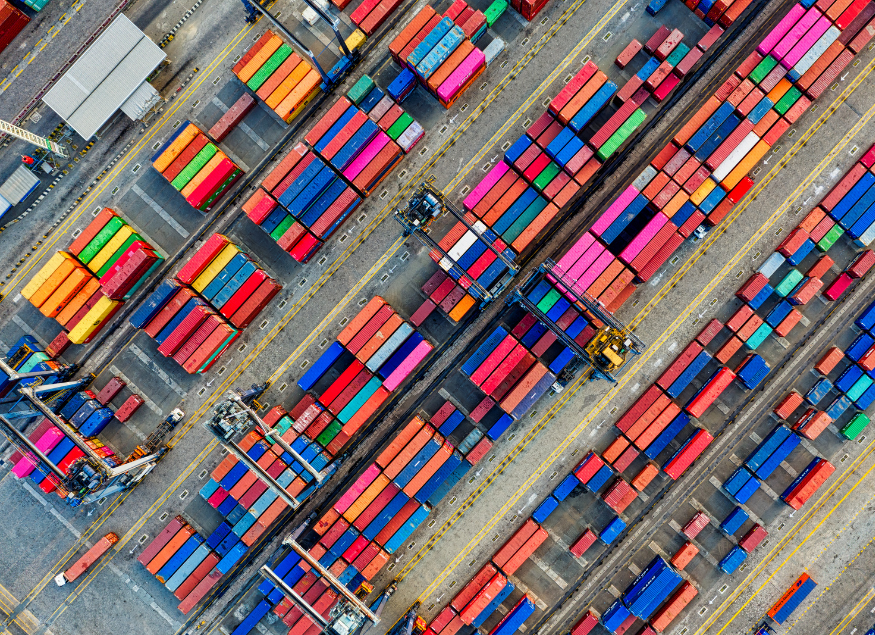
Why Supply Chain Risk Management is Now a Public Sector Resilience Priority
Learn how NIST supply chain risk management helps public sector organizations reduce vendor risk, improve cybersecurity and maintain public trust.
How AI is Reshaping Courts and Legal Operations
AI in the legal system is shifting from theory to practice as courts adopt responsible tools to improve efficiency, access to justice and operations.
Weathering the Storm: Migrating to the Cloud in Government
Learn how Government agencies can weather cloud migration challenges and modernize IT with expert strategies from the CarahCast podcast.
Top 10 DevSecOps Events for Government in 2026
Check out Carahsoft's inclusive list of the top DevSecOps events for 2026 and learn more about our partners' involvement.
The Federal 100 Signals Optimization in Federal IT
How the Federal 100 highlights shifting federal IT priorities, revealing the move toward optimization, enterprise alignment and measurable mission impact across agencies.
10 Healthcare Technology Predictions Shaping 2026
Discover 10 healthcare IT trends shaping 2026, from interoperability to data-driven care and how Carahsoft helps providers streamline outcomes.
Top 10 Quantum Events for Government in 2026
Check out Carahsoft's inclusive list of the top Quantum events for 2026 and learn more about our partners' involvement.
Top 10 FedRAMP Events for Government in 2026
Check out Carahsoft's inclusive list of the top FedRAMP events for 2026 and learn more about our partners' involvement.
Join Our Community
Partner Insights
-
Unified Financial Intelligence: Why Government Finance Teams Have a Data Foundation Problem, Not a Data Problem
Learn how Incorta, Google and Carahsoft help Public Sector agencies modernize finance, accelerate close cycles and deliver real-time, AI-ready insights.