One of the first challenges in combatting ransomware is recognizing the imminence of an attack and the impact it could have on an individual’s personal organization. For 60% of companies surveyed by ActualTech Media and Ransomeware.org, they reported spending zero to four hours on ransomware preparedness per month.[1] Getting collective buy-in from administrators can be difficult since the cybersecurity measures put into place cannot show their full value without being hit by a ransomware attack; however, when compared to the number and scale of attacks occurring, greater attention to cybersecurity is imperative. The NIST Cybersecurity Framework (CSF) provides a guiding set of principles that inform strategies for mitigating ransomware risk. Addressing ransomware starts with identification of a security program followed by protection, prevention, detection, recovery and then security improvements. Ideally companies would follow this CSF outline but in reality, for most organizations the path looks different. Due to feasibility and order of highest critical priority, many companies first establish detection and recovery methods followed by protection, prevention, and security improvement.
RANSOMWARE DETECTION AND RECOVERY
When ransomware hits an organization, the biggest immediate concern is finding the problem and returning to business operations as usual. Many resources exist to assist with this endeavor including asset management tools that automatically inventory all devices on the network and monitor for potential ways malware can get in. Implementing edge detection allows companies to be alerted and quickly identify early on if the network has been compromised and which accounts and devices require isolation and additional measures to prevent the further spread to other servers, accounts and storage units. Anti-virus programs are also helpful to monitor endpoints for indicators of compromise or malware. By achieving early detection, companies can contain the malware and reduce data loss.[2] It also aids in preventing extended downtime which is very costly for operations and business reputation. Apart from the actual ransom, the downtime alone caused by cyberattacks in 2020 cost $20.9 billion to American businesses.[1]
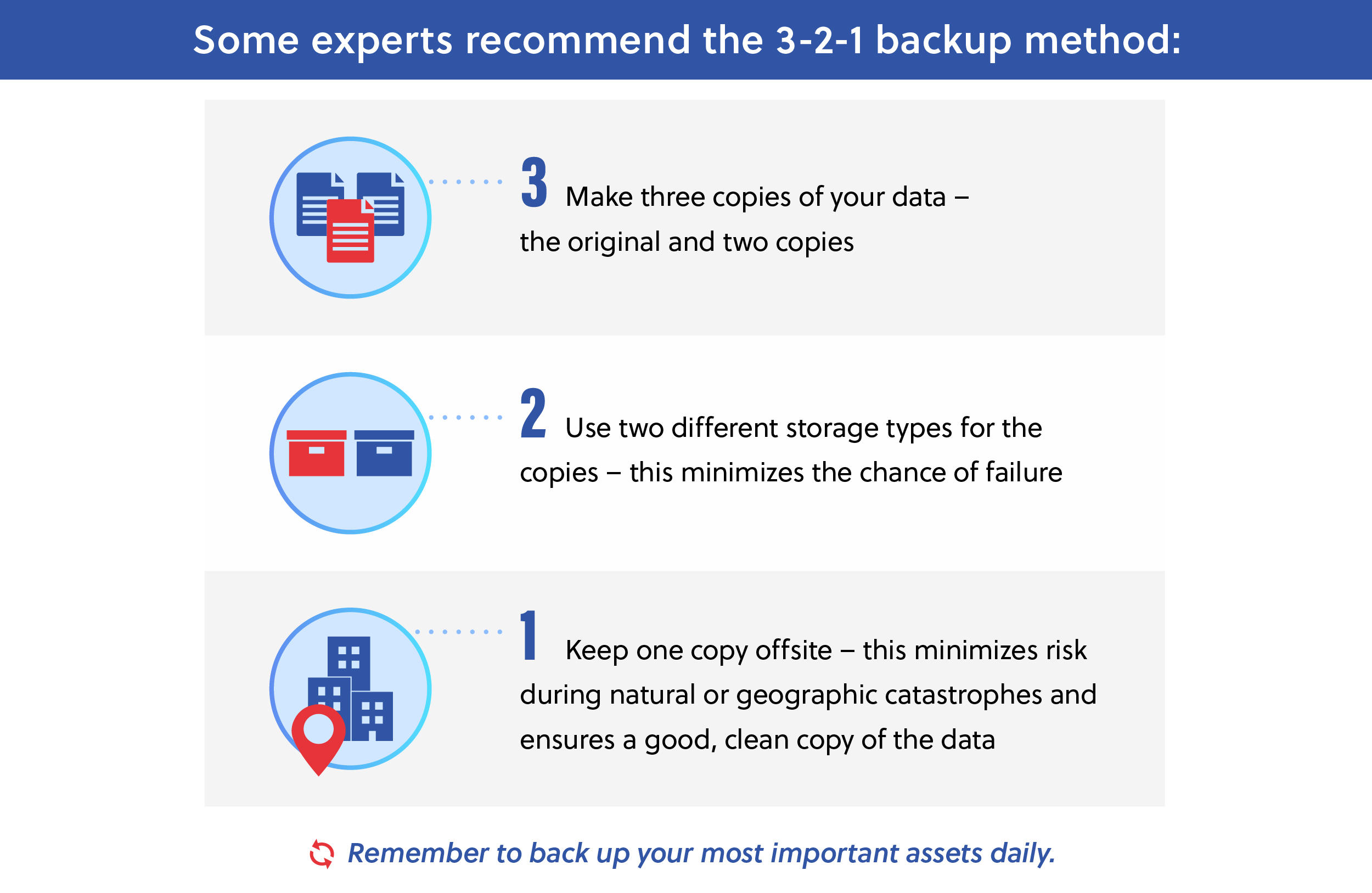
Once malware has been detected, a company’s recovery plan and preparation are put to the test. IT specialists and company administrators need to have an emergency plan in place so there are straightforward steps to recovery. Backups not only need to be created and stored off-site, but also updated on a regular basis and tested to ensure that they are a solid base for a system restoration. With most traditional backup systems, the data cannot be recovered fast enough to neutralize the ransomware’s impact on operations. Instead, a new strategy must be adopted that shifts from 200,000 files taking eight plus hours to restore via the traditional backups, to millions of files being recovered in minutes. Granular, immutable, verifiable snapshots are required to successfully recover all of an organization’s data.[2]
The Sophos “State of Ransomware” report indicated that 77% of healthcare organizations that did not experience a ransomware attack in 2021 attributed it to efforts such as backups and cyber insurance, which help with remediation but not prevention. This exposed an ongoing misunderstanding within the industry on cybersecurity methods.[3] Obtaining cyber-insurance does not prevent future attacks; however, instituting proper security strategies does decrease the susceptibility to ransomware. Recovery tools and insurance provide support during post-breach response but ultimately, in conjunction, organizations should strive to prevent the attack in the first place which requires implementing protection and prevention. According to the Government Accountability Office (GAO), cyber-insurance is a valuable resource to employ but noted that it is increasingly harder to acquire, due to the massive volume of cyberattacks, a higher bar of entry and more requirements to gain coverage and receive payouts. This leaves organizations who do not have sufficient security or insurance to face the recovery process and expensive remediation costs alone.[4]
RANSOMWARE PROTECTION AND PREVENTION
While most organizations invest in attack detection and recovery strategies, the protection aspect of the NIST CSF is equally important and an essential element to reduce the amount of recovery needed. Protection and prevention of ransomware attacks begins with establishing system routines and measures that make it more difficult for hackers to infiltrate. Through implementing Zero Trust user principles such as Multi-Factor Authentication (MFA), institutions and agencies can protect themselves by verifying the identity of employees. Poor password hygiene is one of the leading gateways to malware infiltration, making thorough employee training and password management software a baseline to reduce risk. The average user has access to over 20 million corporate files, making each employee a critical part of keeping the network safe and a huge liability if they are not vigilant and following best practices.[2] Segmentation of the network to provide user-specific access to data and system resources also creates safety barriers, so in the event of an attack the entire network is not automatically compromised. Around 80% of critical infrastructure companies without Zero Trust policies experience an $1.17 million increase in breach costs bringing to an average of $5.4 million per attack in 2022.[5]
Comprehensive Zero Trust authentication and data access control to limit complete access to the entire company’s files is a first step in this process. File indexing, which classifies the level of sensitivity of information contained, allows companies to better allocate resources to prioritize their protection of the most important or confidential files.[2] When processes are automated through these and other resources, it eases IT teams’ responsibilities and reduces the chance of error. Incorporating artificial intelligence (AI) and machine learning (ML) also expedites the identification of confidential information with metadata tags, along with advanced detection of suspicious network and user activity, and thereby minimizes inefficiencies.[6]
Organizations must rigorously search for security gaps and proactively work to close them. Some other measures to incorporate include:
- Filtering for phishing emails and providing awareness training to minimize the possibility of a user accidentally clicking a malicious link
- Utilizing firewalls to block unusual network traffic and segment the network to impede malware system communications
- Monitoring software licenses to ensure they are updated and systems are adequately patched
- Removing expired and extraneous user credentials and unused legacy technology
- Tracking vulnerabilities on devices like IoTs, OTs, and employees’ personal devices used for work (BYODs) throughout the entire connection lifecycle
- Implementing Zero Trust cloud security with container scanning and proxies like a Cloud Access Security Broker (CASB) and Zero Trust Network Access (ZTNA)
RANSOMWARE SECURITY IMPROVEMENT
Following an attack, companies have the opportunity to grow and improve from the situation as well as share resources with other public and private sector companies to strengthen defenses. Incident reporting is a key strategy to prevent future ransomware incidents and a top priority for the Cybersecurity and Infrastructure Security Agency (CISA). Agencies and organizations must support each other to defend against these cyber threats that affect every industry.[7]
To support this greater focus on information sharing, the Cyber Incident Reporting for Critical Infrastructure Act of 2022 took effect in March requiring a more stringent timeline and adherence to disclosing cybersecurity attacks and ransomware payments to the government. CISA also now has the authority to subpoena critical infrastructure organizations if they do not report any cybersecurity incidents within 72 hours of a cyberattack and 24 hours of a ransom payment.[8]
This threat information sharing requirement along with other recent rules on reporting attack incidents strengthen organizations’ security posture and reduce the success rates of cyberattacks. Through these joint efforts and public-private partnerships, companies can recover faster, resume normal operations and support other businesses in the defense of their industry and the nation.[9]
To assist with incorporating these cybersecurity best practices, Congress passed the Infrastructure Investment and Jobs Act Public Law 117–58 which offers $2 billion to “modernize and secure federal, state, and local IT and networks; protect critical infrastructure and utilities; and support public or private entities as they respond to and recover from significant cyberattacks and breaches.”[10]
RANSOMWARE RISK MITIGATION
Tech modernization, while crucial to agencies and organizations’ survival and growth, also presents unique challenges in protecting those technologies.[11] In their journey to securing their legacy and updated systems, companies must take the time to honestly evaluate their cybersecurity standing across the ransomware cycle and ensure their readiness to handle an attack. Utilizing NIST CSF security strategies and other resources help organizations to mitigate risk and empower other companies to learn and protect their systems. By implementing best practices and technologies to address cyber hacks and data breaches, companies are valuing both their customers and their own bottom line. Proactive cybersecurity measures are key for all companies to stem the tide of ransomware attacks and protect the continued growth of their organizations.
Learn about the current state of ransomware and its impact across sectors in our Ransomware Series. Visit our website to learn how Carahsoft and its partners are providing solutions to assist in the fight against ransomware.
Resources:
[1] “Everything You Need to Know About Ransomware,” Ransomware.org, https://ransomware.org/
[2] “Protect, Detect & Recover: The Three Prongs of a Ransomware Defense Strategy for Your Enterprise Files,” Nasuni, https://media.erepublic.com/document/Whitepaper-_A_Three_Prong_Ransomware_Strategy_-_Nasuni.pdf
[3] “The State of Ransomware in Healthcare 2022,” Sophos, https://news.sophos.com/en-us/2022/06/01/the-state-of-ransomware-in-healthcare-2022/
[4] “Healthcare data breach costs reach record high at $10M per attack: IBM report,” Fierce Healthcare, https://www.fiercehealthcare.com/health-tech/healthcare-data-breach-costs-reach-record-high-10m-attack-ibm-report
[5] “Cyber Attacks Against Critical Infrastructure Quietly Increase,” Government Technology, https://www.govtech.com/blogs/lohrmann-on-cybersecurity/cyber-attacks-against-critical-infrastructure-quietly-increase
[6] “Four Best Practices for Protecting Data Wherever it Exists,” Dell Technologies and Carahsoft, https://www.carahsoft.com/2nd-page/dell-4-best-practices-federal-data-security-protection-report-2022#page=4
[7] “Ransomware Hackers Will Still Target Smaller Critical Infrastructure, CISA Director Warns,” Nextgov, https://www.nextgov.com/cybersecurity/2022/07/ransomware-hackers-will-still-target-smaller-critical-infrastructure-cisa-director-warns/374953/
[8] “DHS Convenes Regulators, Law Enforcement Agencies on Cyber Incident Reporting,” Nextgov, https://www.nextgov.com/cybersecurity/2022/07/dhs-convenes-regulators-law-enforcement-agencies-cyber-incident-reporting/374968/
[9] “Ransomware Attacks on Hospitals Have Changed,” AHA Center for Health Innovation, https://www.aha.org/center/cybersecurity-and-risk-advisory-services/ransomware-attacks-hospitals-have-changed
[10] “FACT SHEET: Top 10 Programs in the Bipartisan Infrastructure Investment and Jobs Act That You May Not Have Heard About.” The White House, https://www.whitehouse.gov/briefing-room/statements-releases/2021/08/03/fact-sheet-top-10-programs-in-the-bipartisan-infrastructure-investment-and-jobs-act-that-you-may-not-have-heard-about/
[11] “Global Data Protection Index 2021,” Dell Technologies, https://www.dell.com/en-us/dt/data-protection/gdpi/index.htm#pdf-overlay=//www.delltechnologies.com/asset/en-us/products/data-protection/industry-market/global-data-protection-index-key-findings.pdf
Infographic Resources:
“Ransomware and Energy and Utilities,” AT&T Cybersecurity, https://cybersecurity.att.com/blogs/security-essentials/ransomware-and-energy-and-utilities







